在安全编码方面保持领先地位。
网络威胁格局在不断变化,保持领先地位比以往任何时候都更加重要。通过一系列视频、博客和便捷的安全编码指南,我们可以帮助您保持最新状态,为下一步做好准备。

我们最新的安全编码指南。
导入 mysql 连接器
db = mysql.connector.conn
#Bad 练习。避免这种情况!这只是为了学习。
(host= “localhost”,user= “新用户”,passwd= “pass”,db= “样本”)
cur = db.cursor ()
name = raw_input ('输入名称:')
cur.execute(“从 sample_data 中选择 * 其中 Name = '%s';”% name)为 cur.fetchall () 中的行:打印(行)
db.close ()
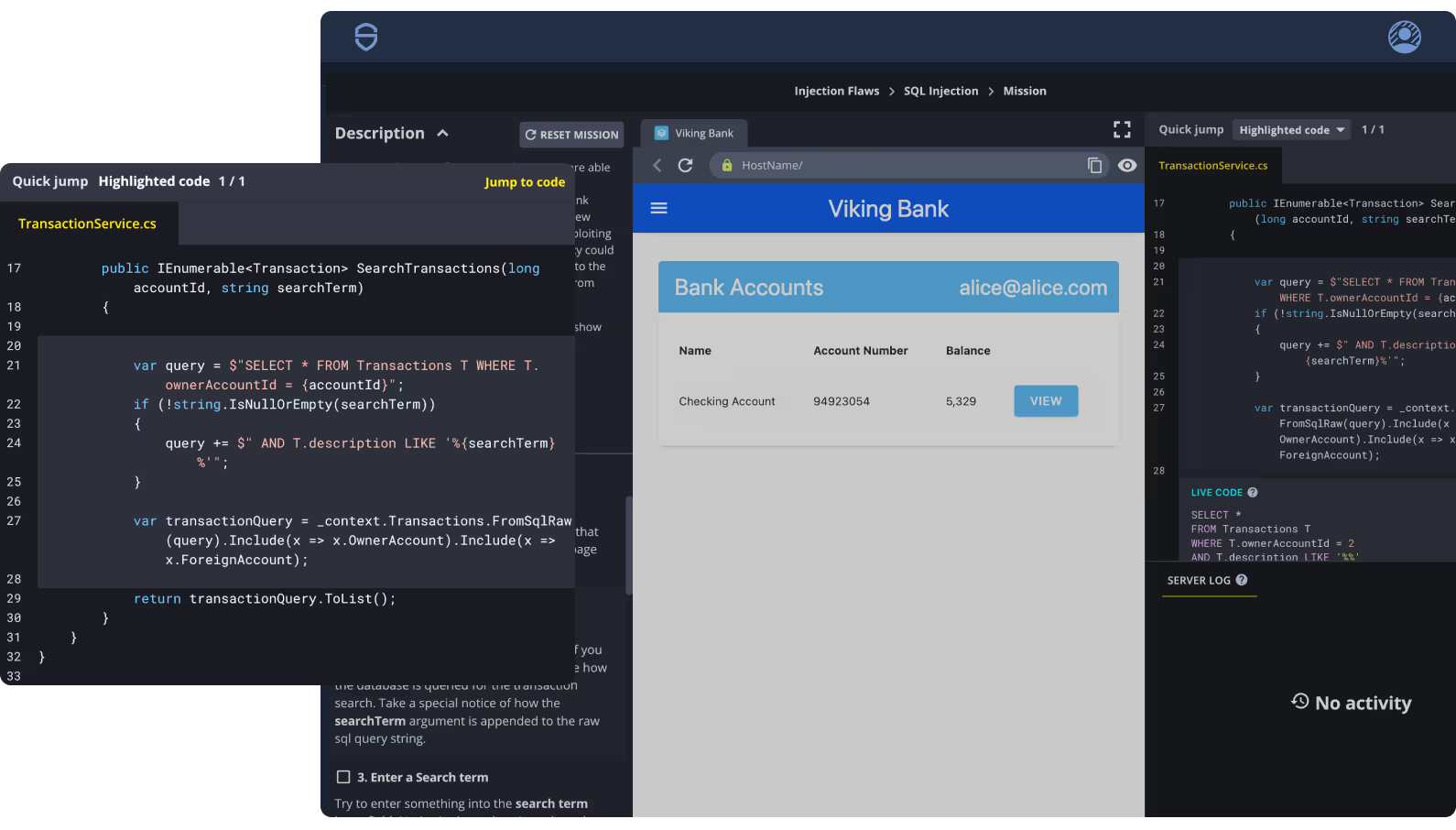
SQL 注入
导入 mysql 连接器
db = mysql.connector.conn
#Bad 练习。避免这种情况!这只是为了学习。
(host= “localhost”,user= “新用户”,passwd= “pass”,db= “样本”)
cur = db.cursor ()
name = raw_input ('输入名称:')
cur.execute(“从 sample_data 中选择 * 其中 Name = '%s';”% name)为 cur.fetchall () 中的行:打印(行)
db.close ()
SQL 注入 (SQLi) 将代码注入到 SQL 语句中,以攻击应用程序并从应用程序收集重要信息。这是一个网络安全漏洞。这是操纵数据库并从中提取关键信息的最常见的黑客技术。

许多框架还具有一组可以启用的端点,无论是在生产环境还是在测试/开发环境中,都可以监控应用程序。这些可能包括:
指标(普罗米修斯)
日志
环境信息
路径/网址映射
ts
让 url = request.params.url;
让响应 = http.get (url);
let render = response.render ();
返回 render.export ();
现实世界中的安全编码任务。
浏览我们的公共培训演习库。这些样本 SCW 任务为您提供有指导的动手体验,包括在真实世界的应用程序模拟中进行一些攻击性的安全编码实践。