Solving the Visibility Crisis: How Trust Agent Bridges the Gap Between Learning and Code

For years, security leaders have invested heavily in secure coding programs, yet a fundamental question remains unanswered: Do we truly know who is committing code, and do they possess the skills required to write, review, and ultimately deliver secure code?
Traditional "shift-left" approaches leave enterprises struggling with massive blind spots when it comes to discovering and onboarding developers for secure coding programs. As program administrators rely on manual checks, spreadsheets and HR org structures to track developer secure coding skills, "shadow developers" who contribute code across critical code bases but lack security proficiency often emerge. This reality severely undermines secure SDLC goals and complicates governance, making it difficult to prove security competency when faced with internal or external reviews.
Secure Code Warrior’s Trust Agent eliminates this risk, transforming your secure coding program into a continuously monitored, verifiable defense that gives CISOs and AppSec leaders the confidence to prove their developers possess the necessary security proficiency required, on every commit.
Continuous Oversight and Assurance with Trust Agent
Without continuous oversight, developer risk remains hidden. Trust Agent delivers ongoing visibility by operationalizing security at the code commit level.
Continuous Developer Discovery: Knowing Your Scope
Before you can secure your codebase, you must know who is touching it.
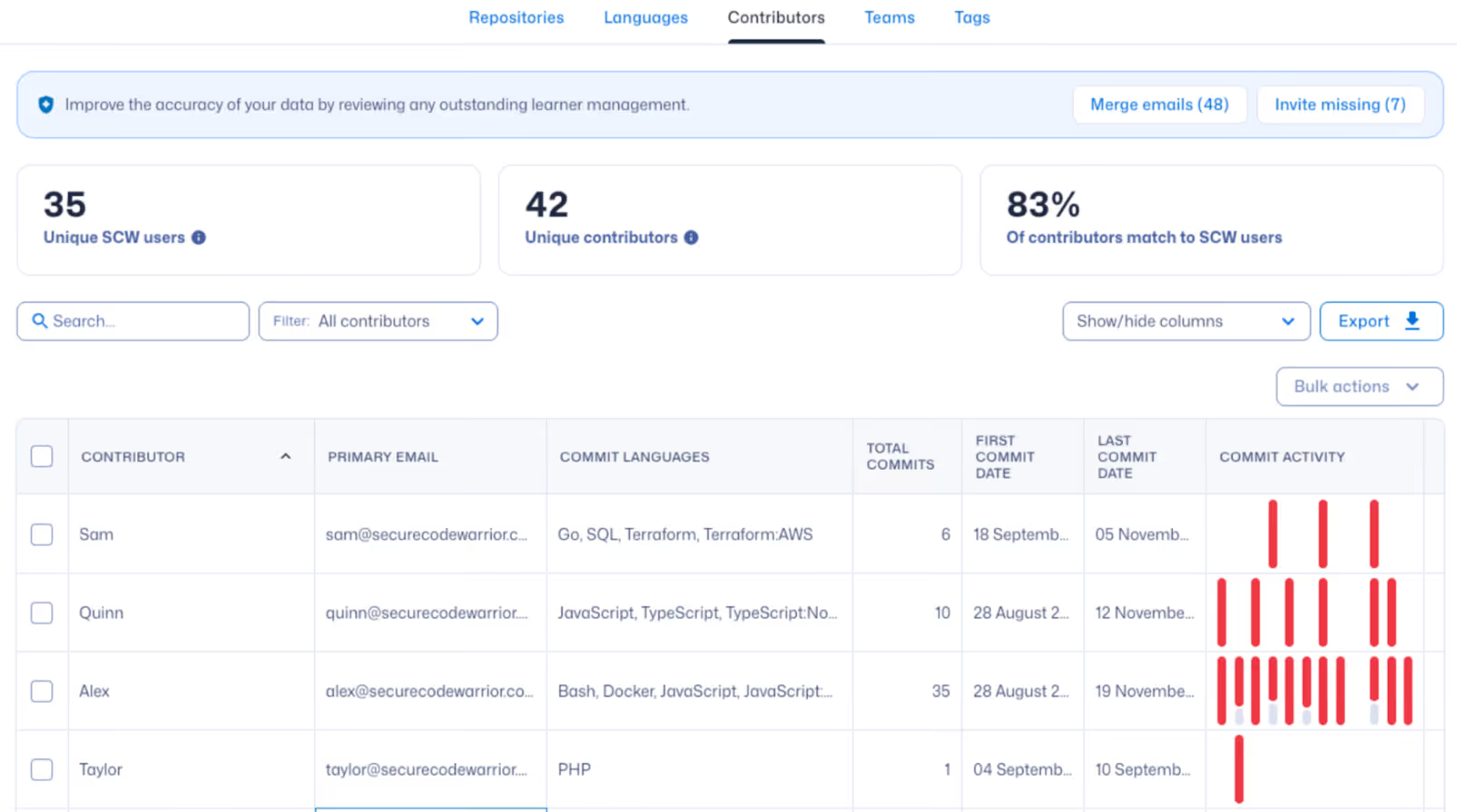
Trust Agent automatically scans your integrated repositories to discover all active code contributors across your entire codebase. This helps address a critical challenge of onboarding - a continuous process - and answers the question: do you know when new engineers or contractors join, and whether they are receiving immediate, relevant secure coding education? By continuously monitoring commits, we ensure every developer is immediately identified and their secure coding journey can begin, eliminating the typical onboarding delays and ensuring comprehensive program scope.
Verified Competency: Monitoring Code, Not Just Learning Completion
In addition to discovering all code contributors, Trust Agent transforms learning data into hard evidence by continuously monitoring secure coding skills applied in real-time. It provides deep observability by correlating every code commit with the developer's verified language-specific secure coding proficiency.
This is crucial for mandates like PCI DSS 4.0 (Requirement 6.2.2), which specifically calls for secure code training every 12 months in the language or framework developers commits code in. Trust Agent gives you the auditable evidence needed to prove that security competency is aligned with the languages and frameworks used in your critical applications.
In addition, Trust Agent provides immediate insights into your risk posture by pinpointing which teams or code repositories have high volumes of commits from developers without adequate security skills. This visibility enables program administrators to easily assign the right education to the right developers based on the most relevant, real-time data.
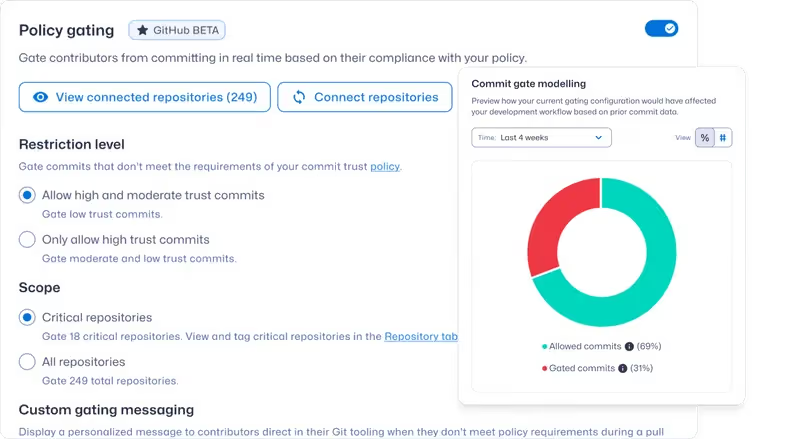
Integrated Governance and Policy Control
Ultimately, governance must be applied to truly lower developer security risk. Trust Agent offers the ability to make security proficiency mandatory by moving controls directly into existing dev workflows, with the ability to define commit policies based on your organization's risk tolerance. Trust Agent automates governance directly in the commit workflow, with policy gates that can be configured to log, warn, or block pull requests if a developer's secure coding skill level is insufficient. This integrated governance is the key to truly ensuring security is a requirement and not an optional suggestion.
Securing the Future of Development
The move to verifiable secure coding proficiency is not just about passing audits- at the end of the day, it’s about shipping innovative, secure code. Even or especially with the rise of AI-assisted development, the fundamental principle remains: developers must be security-proficient to truly lower risk. By making developer secure coding competency a measurable requirement, SCW Trust Agent is the critical piece that ensures your organization not only meets compliance and regulatory obligations, but fundamentally strengthens its security posture from within.
To learn more, book a demo or reach out to your Customer Success Manager today!
Govern AI-driven development before it ships
Measure AI-assisted risk, enforce secure coding policy at commit, and accelerate secure delivery across your SDLC.
Explore more blogs
Lorem Issum diam quis eim leboutis ein selerisque lobortis sepitis beelrisque lobortis sepitis celerisque lobortis celeriskue filmentis celeriskue filmentis celeriskue diam

Security as culture: How Blue Prism cultivates world-class secure developers
Learn how Blue Prism, the global leader in intelligent automation for the enterprise, used Secure Code Warrior's agile learning platform to create a security-first culture with their developers, achieve their business goals, and ship secure code at speed

One Culture of Security: How Sage built their security champions program with agile secure code learning
Discover how Sage enhanced security with a flexible, relationship-focused approach, creating 200+ security champions and achieving measurable risk reduction.
Observe and Secure the ADLC: A Four-Point Framework for CISOs and Development Teams Using AI
While development teams look to make the most of GenAI’s undeniable benefits, we’d like to propose a four-point foundational framework that will allow security leaders to deploy AI coding tools and agents with a higher, more relevant standard of security best practices. It details exactly what enterprises can do to ensure safe, secure code development right now, and as agentic AI becomes an even bigger factor in the future.
Secure AI-driven development before it ships
See developer risk, enforce policy, and prevent vulnerabilities across your software development lifecycle.

%252520%252520(3).avif)

