
高度なセキュリティインテリジェンス:開発者がNISTに対応できるよう支援するガイド付きコース
There have been some very welcome movements in the cybersecurity industry of late. It seems that sentiment around prioritizing security in software builds, as early as possible, is starting to improve in many organizations. This, coupled with official measures like Biden’s Executive Order on cybersecurity, has made it abundantly clear that everyone needs to be doing their part to ensure software security and data safety. What is especially exciting is that the conversation around the role of the developer in maintaining secure coding standards continues to evolve, even at the government level.
However, there is something missing from the conversation. The Executive Order suggests that developers need verified security skills, yet no such official certification currently exists. Many companies remain guided by NIST (who provided updated guidelines in response to the EO) in their quest for compliance and higher standards of software security, but if we’re thinking of strategies to significantly reduce vulnerabilities, while incorporating the right tools and maintaining release velocity, most are simply too generic to create the desired outcome. This is where a lot of companies become unstuck, persevering with limited developer training, or not building upon general foundations to enable them with practical, hands-on skills.
Security-aware developers do not grow on trees, but they can be nurtured and elevated much quicker with the right tools. To that end, we’re pleased to announce our own proprietary course for NIST compliance, as structured by the guidelines of the US Government’s Executive Order.
Meaningful, code-level support for developers
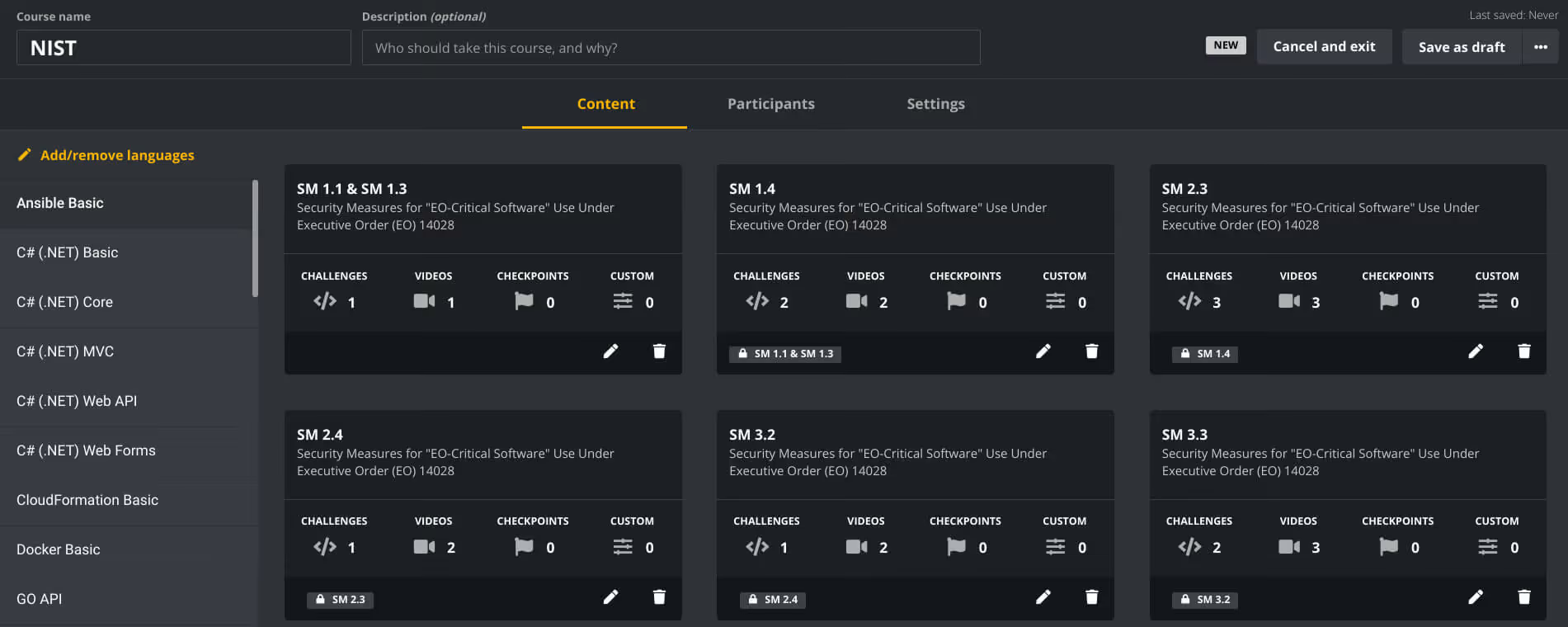
Using the NIST guidelines for Executive Order-critical (EO-critical) software here, we structured the course to hit the five key objectives that will, ultimately, improve the security of vital software in use at the highest levels of government, and should ideally act as a benchmark for higher quality development from the ground up.
For true cut-through in a development cohort, any upskilling must go beyond theory, and be implemented in a way that doesn’t result in constant context-switching between work and training to find answers and stay agile. Meticulous security practices (not to mention the security team) are seen as blockers to on-time development sprints, and seriously cramp the style of the average feature-focused engineer.
Short, snackable micro-learnings that are custom-fit to developer needs get a far less frosty reception, and result in memorable, practical skill-building.
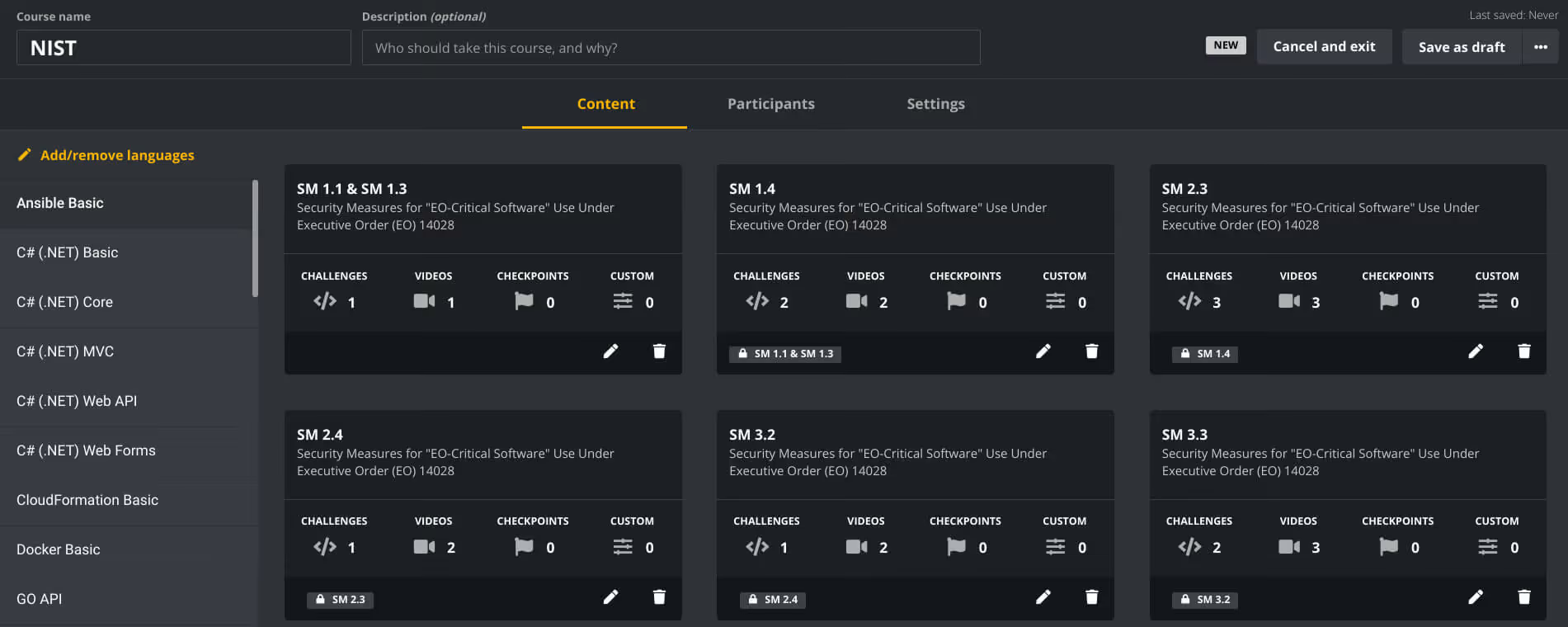
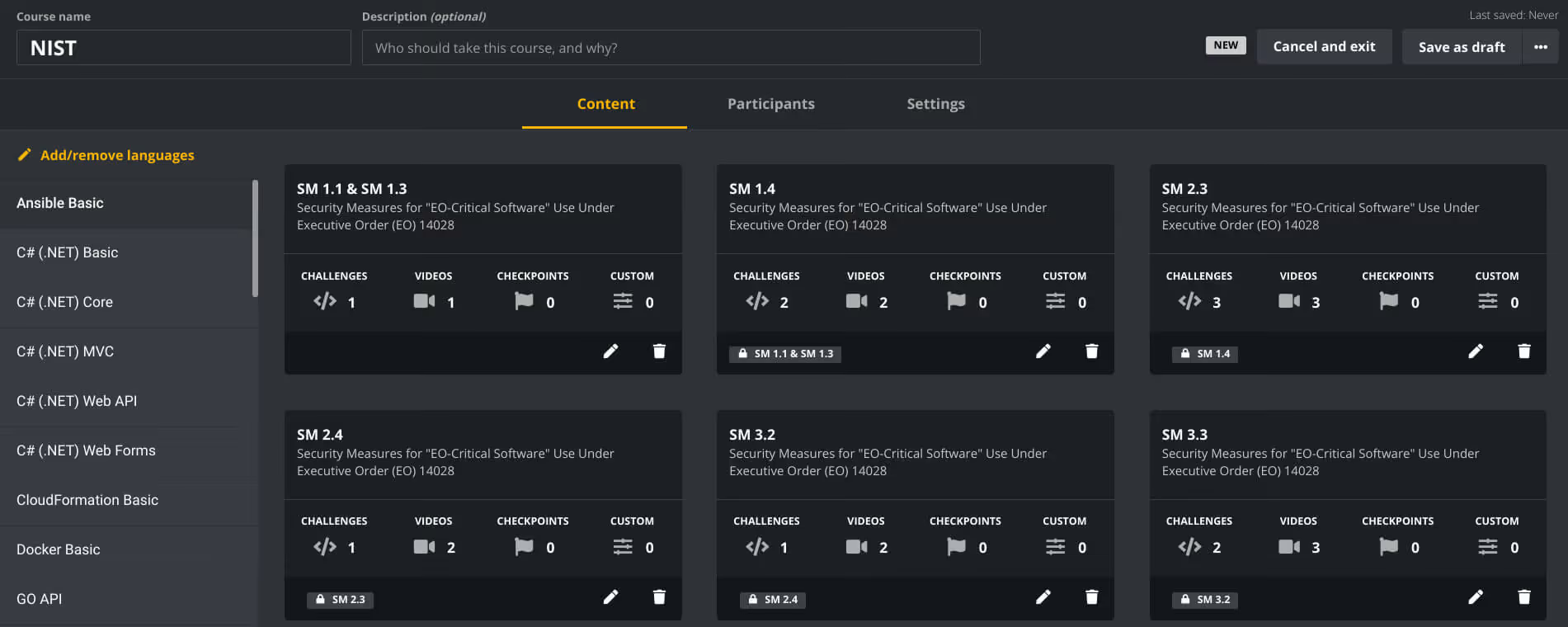
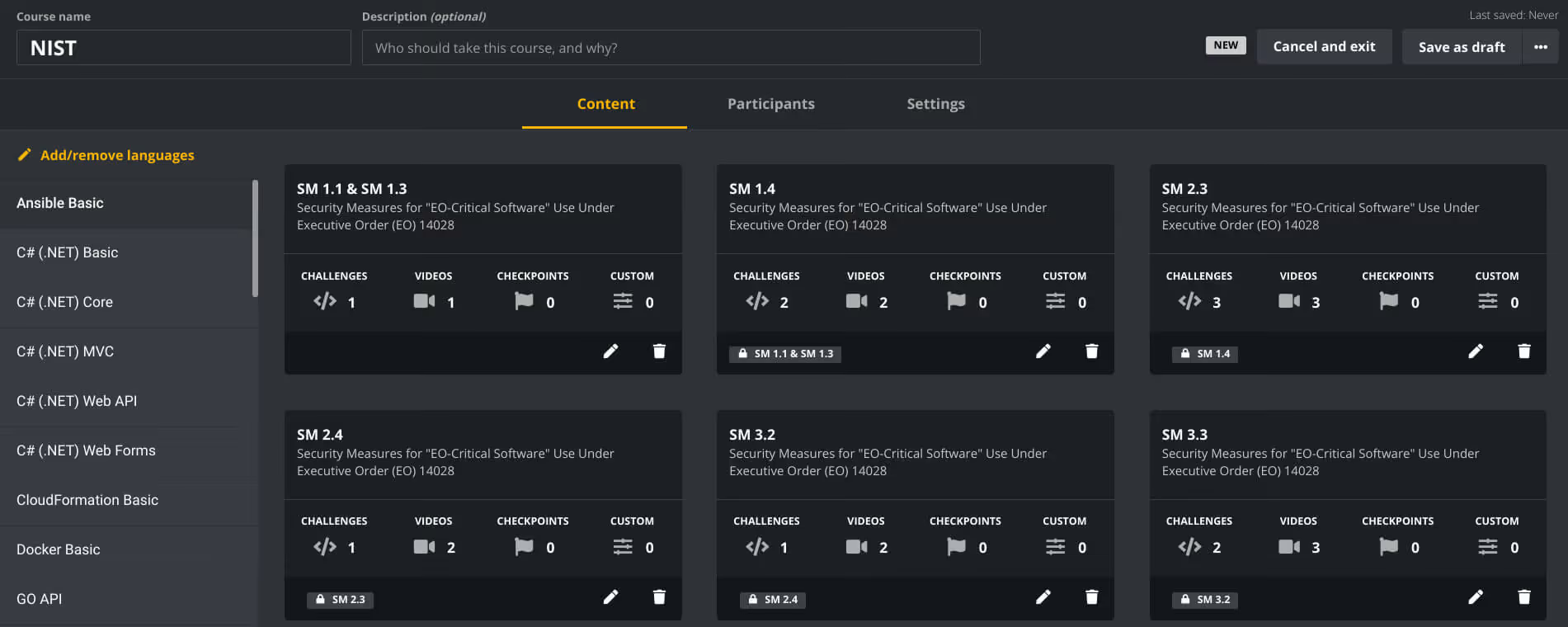
Take a look at how we’ve structured this for our NIST course:
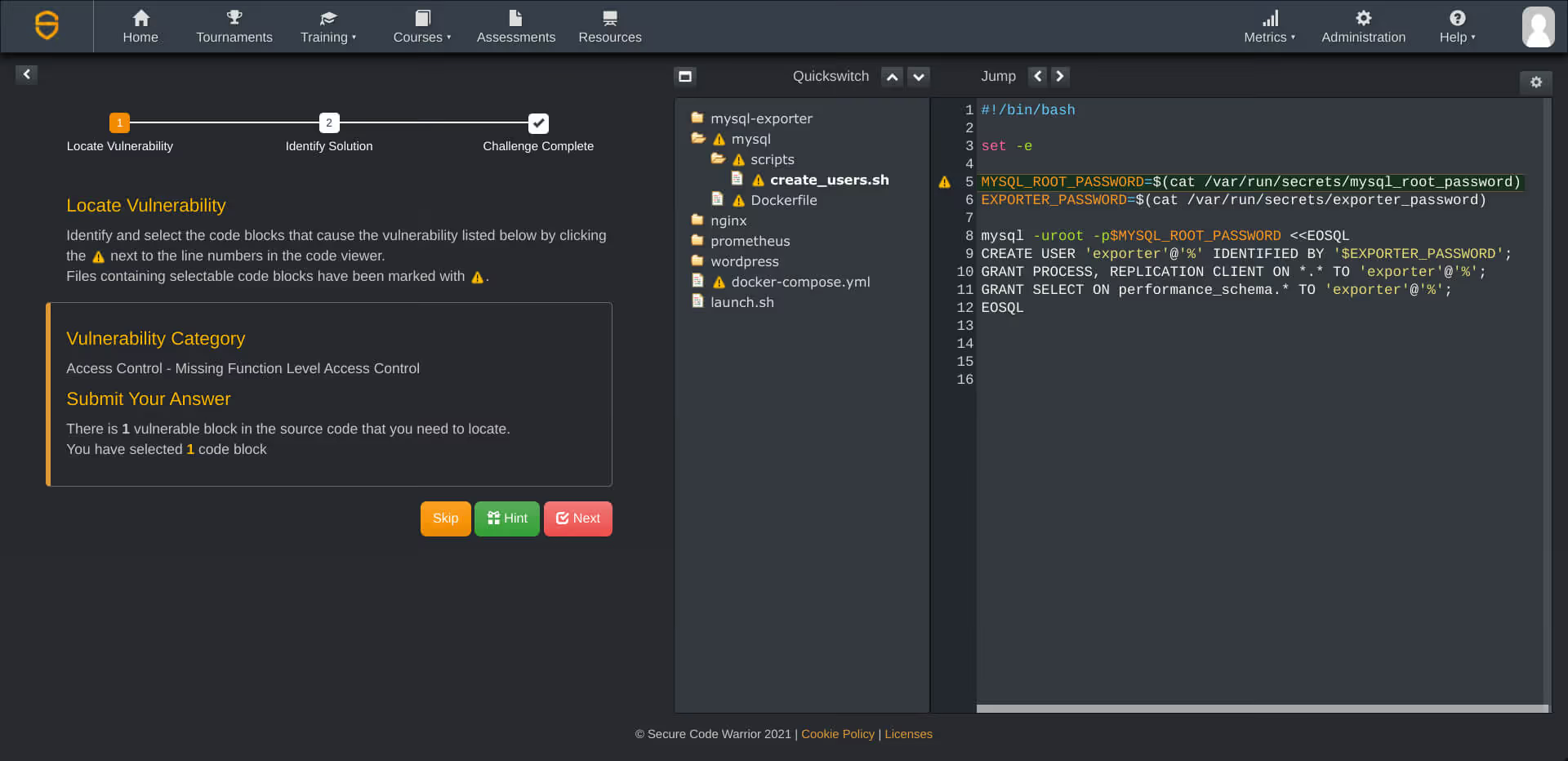
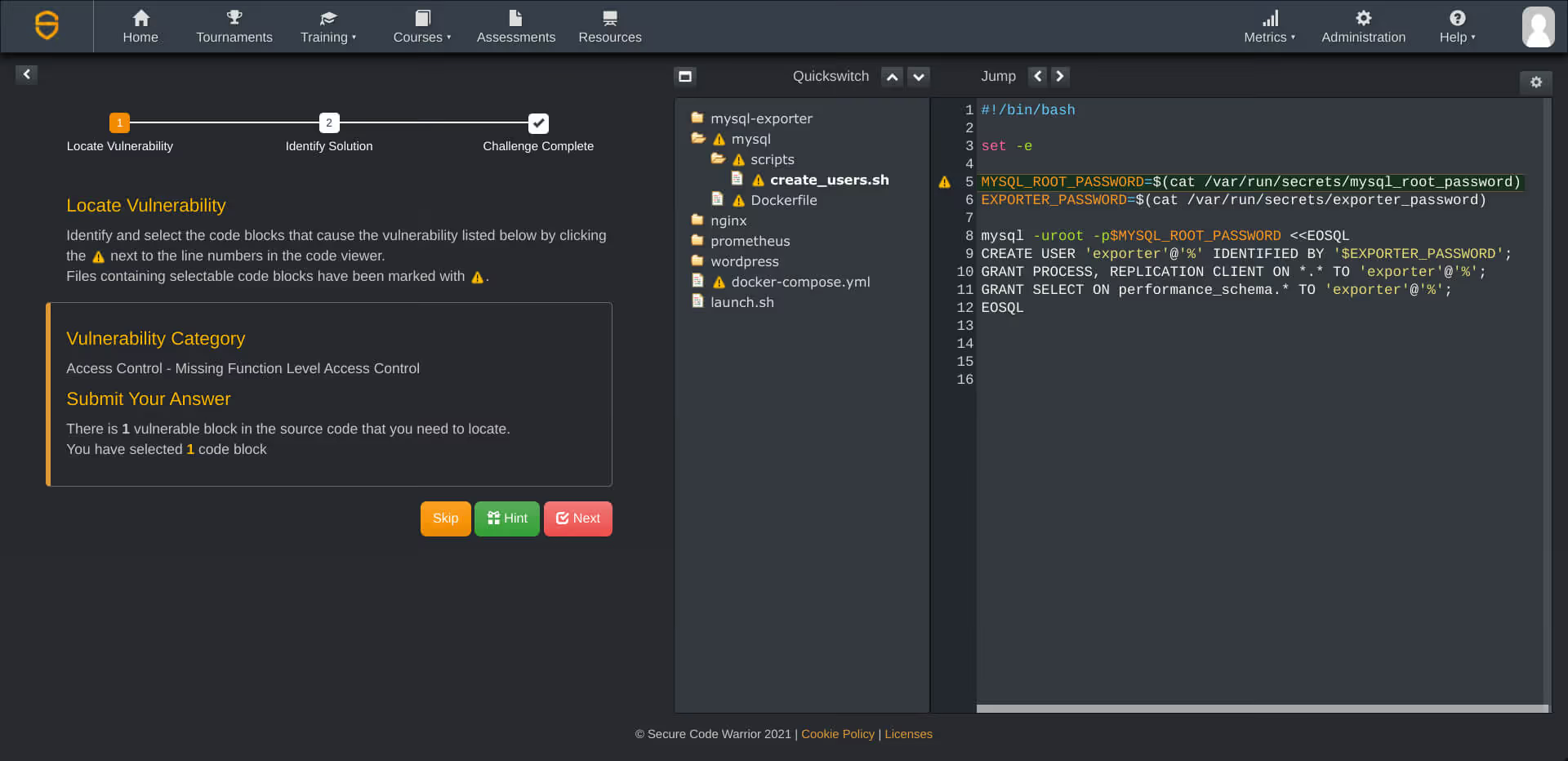
Objective 1: Protect EO-critical software and EO-critical software platforms from unauthorized access and usage.
Security misconfiguration and improper authentication practices are relied upon by attackers to successfully infiltrate systems, take over accounts, and steal data. They are a common bug that can lead to huge problems if successfully exploited.
On the Secure Code Warrior Learning Platform, developers can play challenges based on real-world code snippets that accurately reflect how these bugs would appear in their everyday work, and get them to find an accurate solution to secure them. For the DevOps engineers, securing infrastructure requires meticulous access control configurations, and there are specialized challenges to meet this requirement in Infrastructure as Code (IaC) languages like Terraform, CloudFormation, and Ansible, as well as the code used in Docker and Kubernetes.
Objective 2: Protect the confidentiality, integrity, and availability of data used by EO-critical software and EO-critical software platforms.
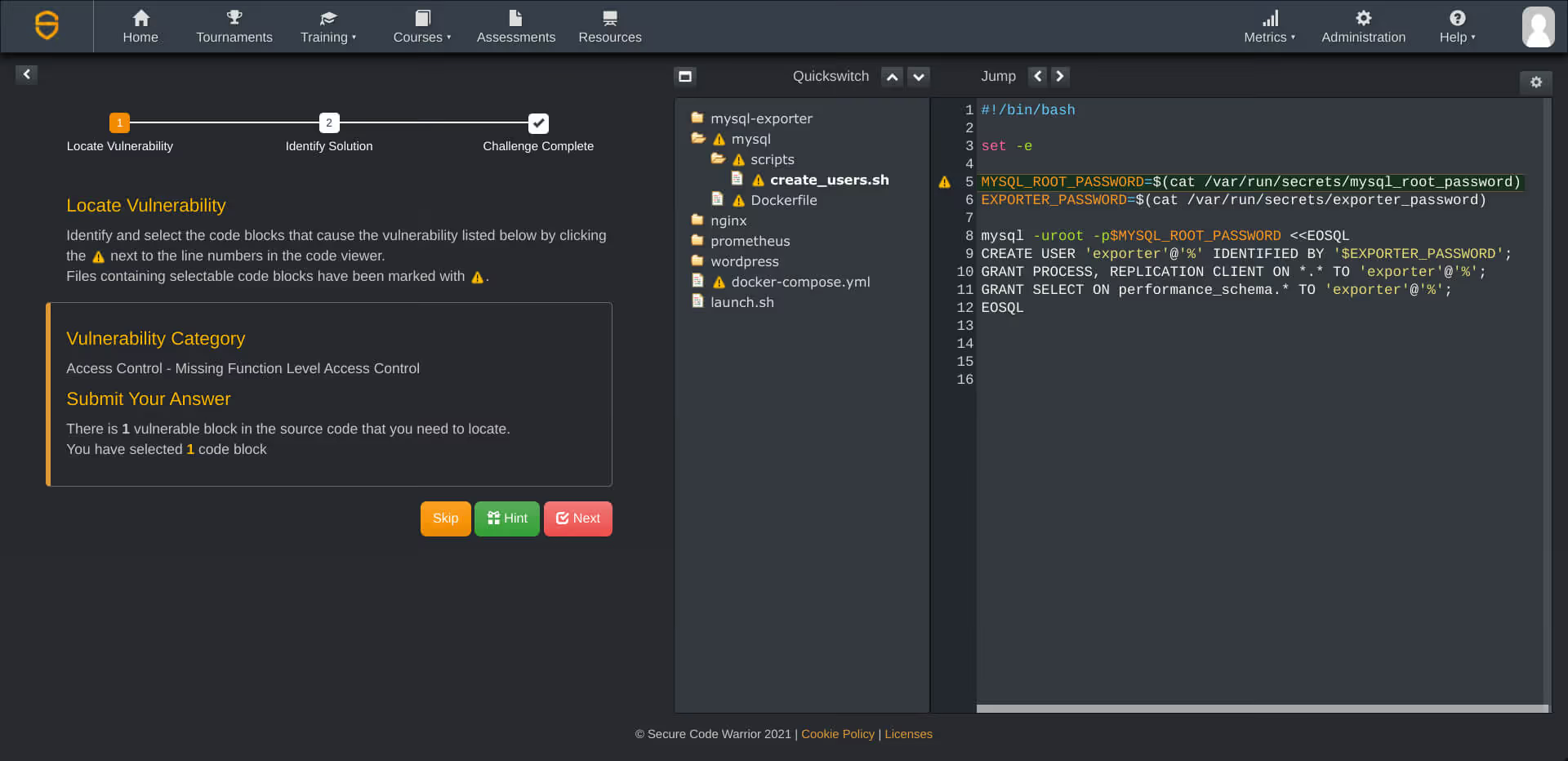
For this objective, all roads lead to access control. Broken access control recently dethroned injection flaws as the top entry in the OWASP Top 10 2021, and it’s a serious bug that requires the skills of security-aware developers to find and fix as early as possible.
The course deals with concepts like least privilege at the code level, and helps instill the approach of limiting access on user accounts to only the necessary areas as best practice.
Objective 3: Identify and maintain EO-critical software platforms and the software deployed to those platforms to protect the EO-critical software from exploitation.
One of the biggest challenges in large organizations is maintaining security oversight on all the different software, systems, and components currently in play. When it comes to risk management and patching, these elements must be a priority in any security program, with developers on high alert to perform security maintenance.
On the Secure Code Warrior Learning Platform, developers can play challenges that will help them identify and fix vulnerable components, as well as permissions-based security misconfiguration.
Objective 4: Quickly detect, respond to, and recover from threats and incidents involving EO-critical software and EO-critical software platforms.
It’s unfortunate (and a waste of time and money) that many organizations still focus on incident response - as opposed to prevention - when dealing with cybersecurity issues. This is a culture that we’re fighting to change, and developers are at the helm of providing preventative firepower when properly trained in security best practices.
Objective 4 requires developers, in the context of their role, to continuously monitor security in their environments, and endpoints both at the software and network level. Insufficient logging and monitoring is another common, insidious bug, and it’s vital that engineers are able to successfully navigate this in their everyday tasks.
On the Secure Code Warrior Learning Platform, developers can play challenges to hone these skills, whether working with web, API, or cloud languages.
Security awareness with sustainability.
Objective 5: Strengthen the understanding and performance of humans’ actions that foster the security of EO-critical software and EO-critical software platforms.
This one is quite generalized, but it’s the most important to achieve… and you can’t do it without mastering the first four objectives. This guideline asks that frequent security awareness activities are carried out, and that all “human actions” on EO-critical software are carried out by those who are adequately trained in the context of their roles and responsibilities.
Developers are among those who are most up close and personal with code, in addition to security configurations and access control. Their security skills must be nurtured, and to achieve the high standards as outlined by NIST, a hands-on course structure might just be the efficient way to tackle it, especially with large development cohorts.
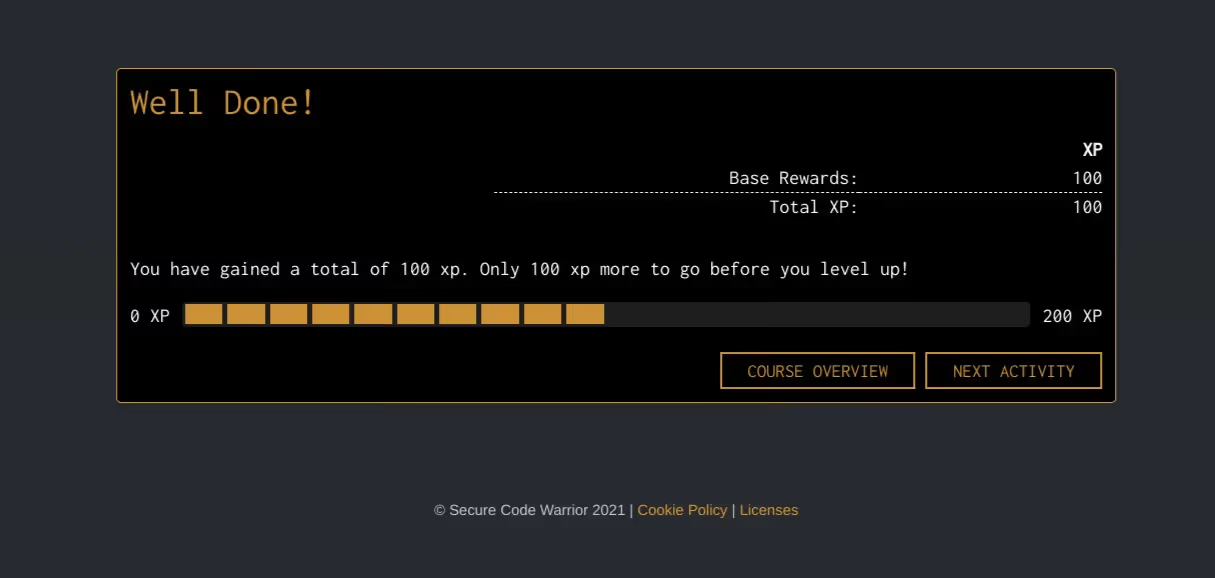
Start adding to your development team’s experience points and security IQ today.


開発者は、セキュリティ設定やアクセス制御に加えて、コードを最も詳しく扱っています。彼らのセキュリティスキルを養う必要があり、NISTが概説しているような高い基準を達成するには、特に大規模な開発コホートでは、実践的なコース構成が効率的な方法かもしれません。
マティアス・マドゥ博士は、セキュリティ専門家、研究者、CTO、セキュア・コード・ウォリアーの共同創設者です。Matias はゲント大学で静的分析ソリューションを中心にアプリケーションセキュリティの博士号を取得しました。その後、米国のFortifyに入社し、開発者が安全なコードを書くのを手伝わずに、コードの問題を検出するだけでは不十分であることに気づきました。これがきっかけで、開発者を支援し、セキュリティの負担を軽減し、顧客の期待を超える製品を開発するようになりました。Team Awesome の一員としてデスクにいないときは、RSA カンファレンス、BlackHat、DefCon などのカンファレンスでプレゼンテーションを行うステージでのプレゼンテーションを楽しんでいます。

Secure Code Warriorは、ソフトウェア開発ライフサイクル全体にわたってコードを保護し、サイバーセキュリティを最優先とする文化を築くお手伝いをします。アプリケーションセキュリティマネージャ、開発者、CISO、またはセキュリティ関係者のいずれであっても、安全でないコードに関連するリスクを軽減するお手伝いをします。
デモを予約マティアス・マドゥ博士は、セキュリティ専門家、研究者、CTO、セキュア・コード・ウォリアーの共同創設者です。Matias はゲント大学で静的分析ソリューションを中心にアプリケーションセキュリティの博士号を取得しました。その後、米国のFortifyに入社し、開発者が安全なコードを書くのを手伝わずに、コードの問題を検出するだけでは不十分であることに気づきました。これがきっかけで、開発者を支援し、セキュリティの負担を軽減し、顧客の期待を超える製品を開発するようになりました。Team Awesome の一員としてデスクにいないときは、RSA カンファレンス、BlackHat、DefCon などのカンファレンスでプレゼンテーションを行うステージでのプレゼンテーションを楽しんでいます。
Matiasは、15年以上のソフトウェアセキュリティの実務経験を持つ研究者および開発者です。フォーティファイ・ソフトウェアや自身の会社であるセンセイ・セキュリティなどの企業向けにソリューションを開発してきました。マティアスはキャリアを通じて、複数のアプリケーションセキュリティ研究プロジェクトを主導し、それが商用製品につながり、10件以上の特許を取得しています。デスクから離れているときには、マティアスは上級アプリケーション・セキュリティ・トレーニング・コースの講師を務め、RSA Conference、Black Hat、DefCon、BSIMM、OWASP AppSec、BruConなどのグローバルカンファレンスで定期的に講演を行っています。
マティアスはゲント大学でコンピューター工学の博士号を取得し、そこでアプリケーションの内部動作を隠すためのプログラムの難読化によるアプリケーションセキュリティを学びました。


There have been some very welcome movements in the cybersecurity industry of late. It seems that sentiment around prioritizing security in software builds, as early as possible, is starting to improve in many organizations. This, coupled with official measures like Biden’s Executive Order on cybersecurity, has made it abundantly clear that everyone needs to be doing their part to ensure software security and data safety. What is especially exciting is that the conversation around the role of the developer in maintaining secure coding standards continues to evolve, even at the government level.
However, there is something missing from the conversation. The Executive Order suggests that developers need verified security skills, yet no such official certification currently exists. Many companies remain guided by NIST (who provided updated guidelines in response to the EO) in their quest for compliance and higher standards of software security, but if we’re thinking of strategies to significantly reduce vulnerabilities, while incorporating the right tools and maintaining release velocity, most are simply too generic to create the desired outcome. This is where a lot of companies become unstuck, persevering with limited developer training, or not building upon general foundations to enable them with practical, hands-on skills.
Security-aware developers do not grow on trees, but they can be nurtured and elevated much quicker with the right tools. To that end, we’re pleased to announce our own proprietary course for NIST compliance, as structured by the guidelines of the US Government’s Executive Order.
Meaningful, code-level support for developers
Using the NIST guidelines for Executive Order-critical (EO-critical) software here, we structured the course to hit the five key objectives that will, ultimately, improve the security of vital software in use at the highest levels of government, and should ideally act as a benchmark for higher quality development from the ground up.
For true cut-through in a development cohort, any upskilling must go beyond theory, and be implemented in a way that doesn’t result in constant context-switching between work and training to find answers and stay agile. Meticulous security practices (not to mention the security team) are seen as blockers to on-time development sprints, and seriously cramp the style of the average feature-focused engineer.
Short, snackable micro-learnings that are custom-fit to developer needs get a far less frosty reception, and result in memorable, practical skill-building.
Take a look at how we’ve structured this for our NIST course:
Objective 1: Protect EO-critical software and EO-critical software platforms from unauthorized access and usage.
Security misconfiguration and improper authentication practices are relied upon by attackers to successfully infiltrate systems, take over accounts, and steal data. They are a common bug that can lead to huge problems if successfully exploited.
On the Secure Code Warrior Learning Platform, developers can play challenges based on real-world code snippets that accurately reflect how these bugs would appear in their everyday work, and get them to find an accurate solution to secure them. For the DevOps engineers, securing infrastructure requires meticulous access control configurations, and there are specialized challenges to meet this requirement in Infrastructure as Code (IaC) languages like Terraform, CloudFormation, and Ansible, as well as the code used in Docker and Kubernetes.
Objective 2: Protect the confidentiality, integrity, and availability of data used by EO-critical software and EO-critical software platforms.
For this objective, all roads lead to access control. Broken access control recently dethroned injection flaws as the top entry in the OWASP Top 10 2021, and it’s a serious bug that requires the skills of security-aware developers to find and fix as early as possible.
The course deals with concepts like least privilege at the code level, and helps instill the approach of limiting access on user accounts to only the necessary areas as best practice.
Objective 3: Identify and maintain EO-critical software platforms and the software deployed to those platforms to protect the EO-critical software from exploitation.
One of the biggest challenges in large organizations is maintaining security oversight on all the different software, systems, and components currently in play. When it comes to risk management and patching, these elements must be a priority in any security program, with developers on high alert to perform security maintenance.
On the Secure Code Warrior Learning Platform, developers can play challenges that will help them identify and fix vulnerable components, as well as permissions-based security misconfiguration.
Objective 4: Quickly detect, respond to, and recover from threats and incidents involving EO-critical software and EO-critical software platforms.
It’s unfortunate (and a waste of time and money) that many organizations still focus on incident response - as opposed to prevention - when dealing with cybersecurity issues. This is a culture that we’re fighting to change, and developers are at the helm of providing preventative firepower when properly trained in security best practices.
Objective 4 requires developers, in the context of their role, to continuously monitor security in their environments, and endpoints both at the software and network level. Insufficient logging and monitoring is another common, insidious bug, and it’s vital that engineers are able to successfully navigate this in their everyday tasks.
On the Secure Code Warrior Learning Platform, developers can play challenges to hone these skills, whether working with web, API, or cloud languages.
Security awareness with sustainability.
Objective 5: Strengthen the understanding and performance of humans’ actions that foster the security of EO-critical software and EO-critical software platforms.
This one is quite generalized, but it’s the most important to achieve… and you can’t do it without mastering the first four objectives. This guideline asks that frequent security awareness activities are carried out, and that all “human actions” on EO-critical software are carried out by those who are adequately trained in the context of their roles and responsibilities.
Developers are among those who are most up close and personal with code, in addition to security configurations and access control. Their security skills must be nurtured, and to achieve the high standards as outlined by NIST, a hands-on course structure might just be the efficient way to tackle it, especially with large development cohorts.
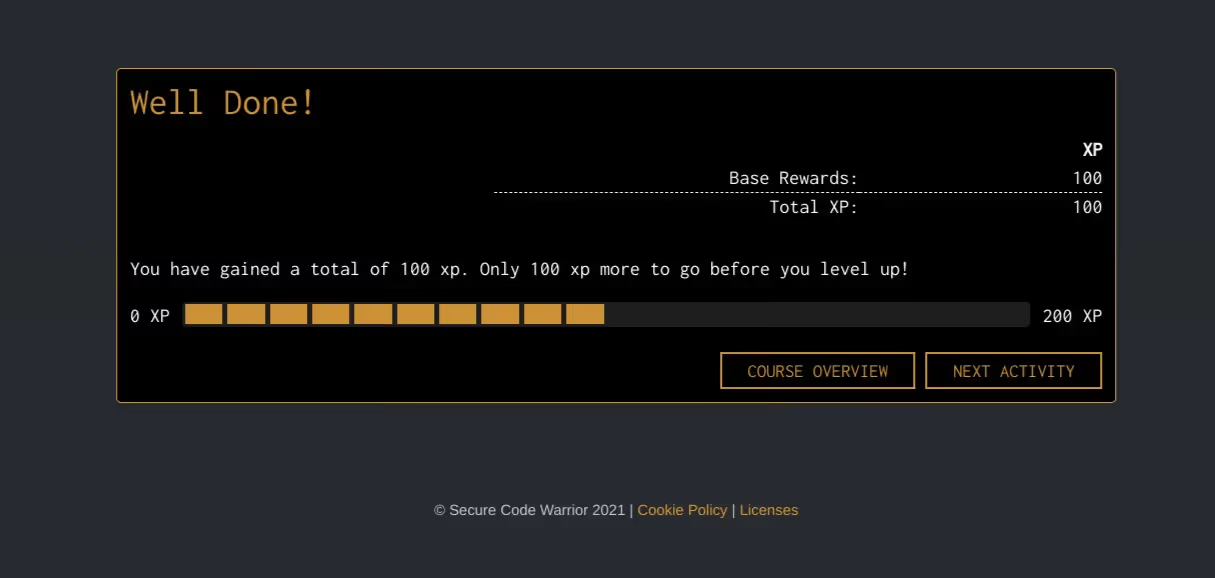
Start adding to your development team’s experience points and security IQ today.

There have been some very welcome movements in the cybersecurity industry of late. It seems that sentiment around prioritizing security in software builds, as early as possible, is starting to improve in many organizations. This, coupled with official measures like Biden’s Executive Order on cybersecurity, has made it abundantly clear that everyone needs to be doing their part to ensure software security and data safety. What is especially exciting is that the conversation around the role of the developer in maintaining secure coding standards continues to evolve, even at the government level.
However, there is something missing from the conversation. The Executive Order suggests that developers need verified security skills, yet no such official certification currently exists. Many companies remain guided by NIST (who provided updated guidelines in response to the EO) in their quest for compliance and higher standards of software security, but if we’re thinking of strategies to significantly reduce vulnerabilities, while incorporating the right tools and maintaining release velocity, most are simply too generic to create the desired outcome. This is where a lot of companies become unstuck, persevering with limited developer training, or not building upon general foundations to enable them with practical, hands-on skills.
Security-aware developers do not grow on trees, but they can be nurtured and elevated much quicker with the right tools. To that end, we’re pleased to announce our own proprietary course for NIST compliance, as structured by the guidelines of the US Government’s Executive Order.
Meaningful, code-level support for developers
Using the NIST guidelines for Executive Order-critical (EO-critical) software here, we structured the course to hit the five key objectives that will, ultimately, improve the security of vital software in use at the highest levels of government, and should ideally act as a benchmark for higher quality development from the ground up.
For true cut-through in a development cohort, any upskilling must go beyond theory, and be implemented in a way that doesn’t result in constant context-switching between work and training to find answers and stay agile. Meticulous security practices (not to mention the security team) are seen as blockers to on-time development sprints, and seriously cramp the style of the average feature-focused engineer.
Short, snackable micro-learnings that are custom-fit to developer needs get a far less frosty reception, and result in memorable, practical skill-building.
Take a look at how we’ve structured this for our NIST course:
Objective 1: Protect EO-critical software and EO-critical software platforms from unauthorized access and usage.
Security misconfiguration and improper authentication practices are relied upon by attackers to successfully infiltrate systems, take over accounts, and steal data. They are a common bug that can lead to huge problems if successfully exploited.
On the Secure Code Warrior Learning Platform, developers can play challenges based on real-world code snippets that accurately reflect how these bugs would appear in their everyday work, and get them to find an accurate solution to secure them. For the DevOps engineers, securing infrastructure requires meticulous access control configurations, and there are specialized challenges to meet this requirement in Infrastructure as Code (IaC) languages like Terraform, CloudFormation, and Ansible, as well as the code used in Docker and Kubernetes.
Objective 2: Protect the confidentiality, integrity, and availability of data used by EO-critical software and EO-critical software platforms.
For this objective, all roads lead to access control. Broken access control recently dethroned injection flaws as the top entry in the OWASP Top 10 2021, and it’s a serious bug that requires the skills of security-aware developers to find and fix as early as possible.
The course deals with concepts like least privilege at the code level, and helps instill the approach of limiting access on user accounts to only the necessary areas as best practice.
Objective 3: Identify and maintain EO-critical software platforms and the software deployed to those platforms to protect the EO-critical software from exploitation.
One of the biggest challenges in large organizations is maintaining security oversight on all the different software, systems, and components currently in play. When it comes to risk management and patching, these elements must be a priority in any security program, with developers on high alert to perform security maintenance.
On the Secure Code Warrior Learning Platform, developers can play challenges that will help them identify and fix vulnerable components, as well as permissions-based security misconfiguration.
Objective 4: Quickly detect, respond to, and recover from threats and incidents involving EO-critical software and EO-critical software platforms.
It’s unfortunate (and a waste of time and money) that many organizations still focus on incident response - as opposed to prevention - when dealing with cybersecurity issues. This is a culture that we’re fighting to change, and developers are at the helm of providing preventative firepower when properly trained in security best practices.
Objective 4 requires developers, in the context of their role, to continuously monitor security in their environments, and endpoints both at the software and network level. Insufficient logging and monitoring is another common, insidious bug, and it’s vital that engineers are able to successfully navigate this in their everyday tasks.
On the Secure Code Warrior Learning Platform, developers can play challenges to hone these skills, whether working with web, API, or cloud languages.
Security awareness with sustainability.
Objective 5: Strengthen the understanding and performance of humans’ actions that foster the security of EO-critical software and EO-critical software platforms.
This one is quite generalized, but it’s the most important to achieve… and you can’t do it without mastering the first four objectives. This guideline asks that frequent security awareness activities are carried out, and that all “human actions” on EO-critical software are carried out by those who are adequately trained in the context of their roles and responsibilities.
Developers are among those who are most up close and personal with code, in addition to security configurations and access control. Their security skills must be nurtured, and to achieve the high standards as outlined by NIST, a hands-on course structure might just be the efficient way to tackle it, especially with large development cohorts.
Start adding to your development team’s experience points and security IQ today.

以下のリンクをクリックして、このリソースのPDFをダウンロードしてください。
Secure Code Warriorは、ソフトウェア開発ライフサイクル全体にわたってコードを保護し、サイバーセキュリティを最優先とする文化を築くお手伝いをします。アプリケーションセキュリティマネージャ、開発者、CISO、またはセキュリティ関係者のいずれであっても、安全でないコードに関連するリスクを軽減するお手伝いをします。
レポートを表示デモを予約マティアス・マドゥ博士は、セキュリティ専門家、研究者、CTO、セキュア・コード・ウォリアーの共同創設者です。Matias はゲント大学で静的分析ソリューションを中心にアプリケーションセキュリティの博士号を取得しました。その後、米国のFortifyに入社し、開発者が安全なコードを書くのを手伝わずに、コードの問題を検出するだけでは不十分であることに気づきました。これがきっかけで、開発者を支援し、セキュリティの負担を軽減し、顧客の期待を超える製品を開発するようになりました。Team Awesome の一員としてデスクにいないときは、RSA カンファレンス、BlackHat、DefCon などのカンファレンスでプレゼンテーションを行うステージでのプレゼンテーションを楽しんでいます。
Matiasは、15年以上のソフトウェアセキュリティの実務経験を持つ研究者および開発者です。フォーティファイ・ソフトウェアや自身の会社であるセンセイ・セキュリティなどの企業向けにソリューションを開発してきました。マティアスはキャリアを通じて、複数のアプリケーションセキュリティ研究プロジェクトを主導し、それが商用製品につながり、10件以上の特許を取得しています。デスクから離れているときには、マティアスは上級アプリケーション・セキュリティ・トレーニング・コースの講師を務め、RSA Conference、Black Hat、DefCon、BSIMM、OWASP AppSec、BruConなどのグローバルカンファレンスで定期的に講演を行っています。
マティアスはゲント大学でコンピューター工学の博士号を取得し、そこでアプリケーションの内部動作を隠すためのプログラムの難読化によるアプリケーションセキュリティを学びました。
There have been some very welcome movements in the cybersecurity industry of late. It seems that sentiment around prioritizing security in software builds, as early as possible, is starting to improve in many organizations. This, coupled with official measures like Biden’s Executive Order on cybersecurity, has made it abundantly clear that everyone needs to be doing their part to ensure software security and data safety. What is especially exciting is that the conversation around the role of the developer in maintaining secure coding standards continues to evolve, even at the government level.
However, there is something missing from the conversation. The Executive Order suggests that developers need verified security skills, yet no such official certification currently exists. Many companies remain guided by NIST (who provided updated guidelines in response to the EO) in their quest for compliance and higher standards of software security, but if we’re thinking of strategies to significantly reduce vulnerabilities, while incorporating the right tools and maintaining release velocity, most are simply too generic to create the desired outcome. This is where a lot of companies become unstuck, persevering with limited developer training, or not building upon general foundations to enable them with practical, hands-on skills.
Security-aware developers do not grow on trees, but they can be nurtured and elevated much quicker with the right tools. To that end, we’re pleased to announce our own proprietary course for NIST compliance, as structured by the guidelines of the US Government’s Executive Order.
Meaningful, code-level support for developers
Using the NIST guidelines for Executive Order-critical (EO-critical) software here, we structured the course to hit the five key objectives that will, ultimately, improve the security of vital software in use at the highest levels of government, and should ideally act as a benchmark for higher quality development from the ground up.
For true cut-through in a development cohort, any upskilling must go beyond theory, and be implemented in a way that doesn’t result in constant context-switching between work and training to find answers and stay agile. Meticulous security practices (not to mention the security team) are seen as blockers to on-time development sprints, and seriously cramp the style of the average feature-focused engineer.
Short, snackable micro-learnings that are custom-fit to developer needs get a far less frosty reception, and result in memorable, practical skill-building.
Take a look at how we’ve structured this for our NIST course:
Objective 1: Protect EO-critical software and EO-critical software platforms from unauthorized access and usage.
Security misconfiguration and improper authentication practices are relied upon by attackers to successfully infiltrate systems, take over accounts, and steal data. They are a common bug that can lead to huge problems if successfully exploited.
On the Secure Code Warrior Learning Platform, developers can play challenges based on real-world code snippets that accurately reflect how these bugs would appear in their everyday work, and get them to find an accurate solution to secure them. For the DevOps engineers, securing infrastructure requires meticulous access control configurations, and there are specialized challenges to meet this requirement in Infrastructure as Code (IaC) languages like Terraform, CloudFormation, and Ansible, as well as the code used in Docker and Kubernetes.
Objective 2: Protect the confidentiality, integrity, and availability of data used by EO-critical software and EO-critical software platforms.
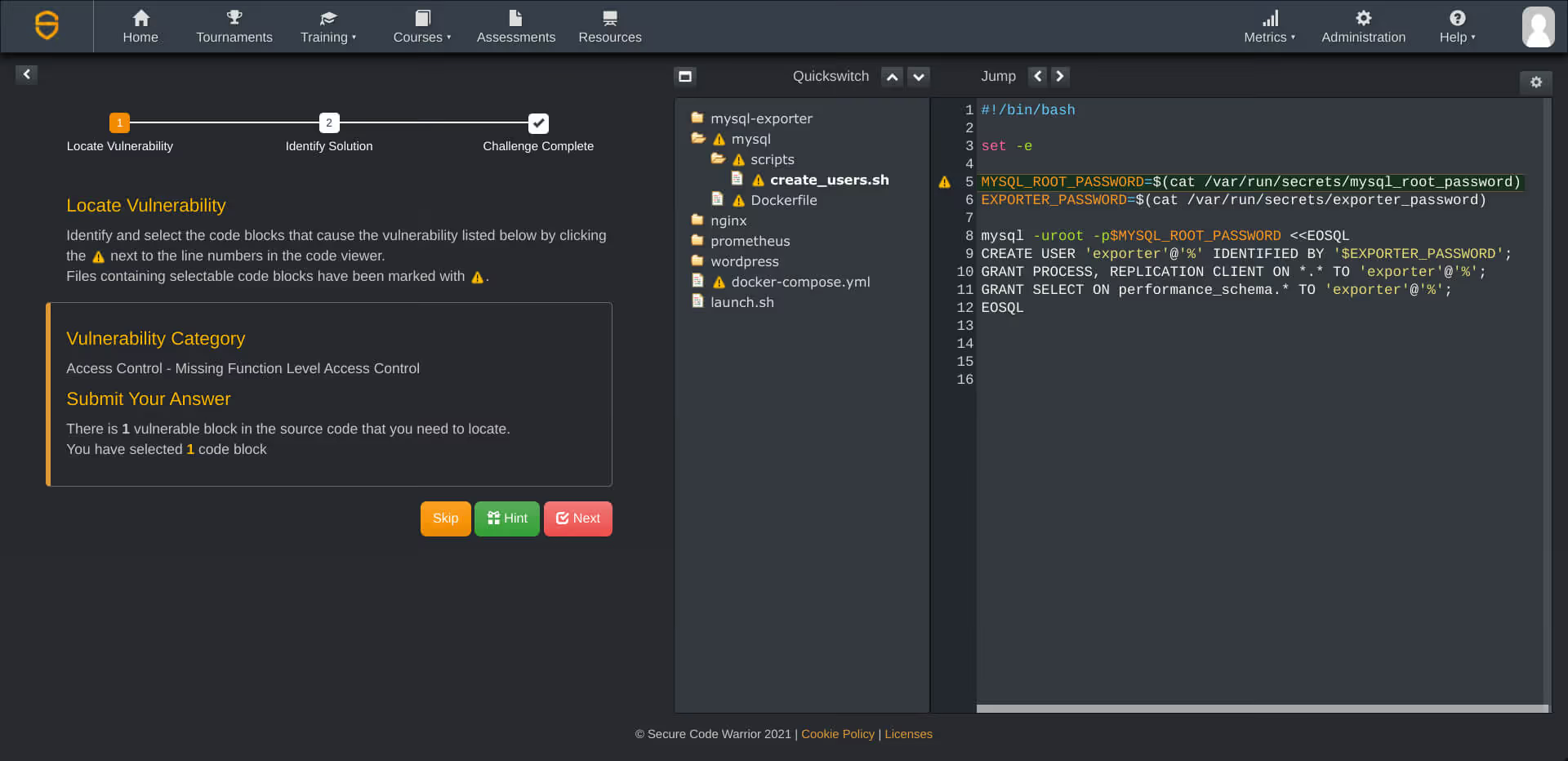
For this objective, all roads lead to access control. Broken access control recently dethroned injection flaws as the top entry in the OWASP Top 10 2021, and it’s a serious bug that requires the skills of security-aware developers to find and fix as early as possible.
The course deals with concepts like least privilege at the code level, and helps instill the approach of limiting access on user accounts to only the necessary areas as best practice.
Objective 3: Identify and maintain EO-critical software platforms and the software deployed to those platforms to protect the EO-critical software from exploitation.
One of the biggest challenges in large organizations is maintaining security oversight on all the different software, systems, and components currently in play. When it comes to risk management and patching, these elements must be a priority in any security program, with developers on high alert to perform security maintenance.
On the Secure Code Warrior Learning Platform, developers can play challenges that will help them identify and fix vulnerable components, as well as permissions-based security misconfiguration.
Objective 4: Quickly detect, respond to, and recover from threats and incidents involving EO-critical software and EO-critical software platforms.
It’s unfortunate (and a waste of time and money) that many organizations still focus on incident response - as opposed to prevention - when dealing with cybersecurity issues. This is a culture that we’re fighting to change, and developers are at the helm of providing preventative firepower when properly trained in security best practices.
Objective 4 requires developers, in the context of their role, to continuously monitor security in their environments, and endpoints both at the software and network level. Insufficient logging and monitoring is another common, insidious bug, and it’s vital that engineers are able to successfully navigate this in their everyday tasks.
On the Secure Code Warrior Learning Platform, developers can play challenges to hone these skills, whether working with web, API, or cloud languages.
Security awareness with sustainability.
Objective 5: Strengthen the understanding and performance of humans’ actions that foster the security of EO-critical software and EO-critical software platforms.
This one is quite generalized, but it’s the most important to achieve… and you can’t do it without mastering the first four objectives. This guideline asks that frequent security awareness activities are carried out, and that all “human actions” on EO-critical software are carried out by those who are adequately trained in the context of their roles and responsibilities.
Developers are among those who are most up close and personal with code, in addition to security configurations and access control. Their security skills must be nurtured, and to achieve the high standards as outlined by NIST, a hands-on course structure might just be the efficient way to tackle it, especially with large development cohorts.
Start adding to your development team’s experience points and security IQ today.
目次
マティアス・マドゥ博士は、セキュリティ専門家、研究者、CTO、セキュア・コード・ウォリアーの共同創設者です。Matias はゲント大学で静的分析ソリューションを中心にアプリケーションセキュリティの博士号を取得しました。その後、米国のFortifyに入社し、開発者が安全なコードを書くのを手伝わずに、コードの問題を検出するだけでは不十分であることに気づきました。これがきっかけで、開発者を支援し、セキュリティの負担を軽減し、顧客の期待を超える製品を開発するようになりました。Team Awesome の一員としてデスクにいないときは、RSA カンファレンス、BlackHat、DefCon などのカンファレンスでプレゼンテーションを行うステージでのプレゼンテーションを楽しんでいます。

Secure Code Warriorは、ソフトウェア開発ライフサイクル全体にわたってコードを保護し、サイバーセキュリティを最優先とする文化を築くお手伝いをします。アプリケーションセキュリティマネージャ、開発者、CISO、またはセキュリティ関係者のいずれであっても、安全でないコードに関連するリスクを軽減するお手伝いをします。
デモを予約[ダウンロード]始めるためのリソース
始めるためのリソース
Secure coding learning that reflects real AI usage
Align secure coding training to real AI development activity — automatically assigning guidance to developers using AI tools, without manual intervention.Align secure coding training to real AI development activity — automatically assigning guidance to developers using AI tools, without manual intervention.
Train developers on the real risks in their code, whether human-written or AI-generated
Adaptive Learning auto-assigns targeted secure coding training to the developers introducing real vulnerabilities, reducing recurring risks at the source.Secure Code Warrior blog banner with a blue overlay over a developer working at a multi-monitor desk displaying code, alongside the headline 'Train developers on the real risks in their code.'l















