Adding Parameters to Annotations Using Rewrite Actions

In this blog post, we will:
- Demonstrate searching and matching annotations
- Amen annotations using mustache templates
Sensei provides the ability to match problematic code patterns and then amend them to agreed implementations. In this example, I am using @Disabled without a parameter as the problematic code pattern.
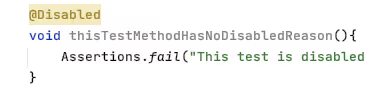
Disabled Test Annotation
Disabled tests without a specified reason can prove problematic over the long term because we forget why we disabled it.
@Disabled
void thisTestMethodHasNoDisabledReason(){
Assertions.fail("This test is disabled and should not run");
}
The risk is that, over time, the code base moves on, the disabled test is not updated in step with the purpose of the code and eventually becomes redundant and irrelevant, and potentially never re-enabled.
During code reviews, we will often point out that it is a good idea to add an explanatory description as the annotation parameter.
@Disabled ("Disabled to demonstrate adding a reason")
void thisTestMethodHasDisabledReason(){
Assertions.fail("This test is disabled and should not run");
}
A Sensei Recipe
We can write a recipe to detect when @Disabled is added without explanation and a Quick Fix that reminds us to add the actual reason explaining why we disabled it.
When I think about what I'm going to do, I have to:
- match the Disabled annotation without any parameters
- change the Disabled annotation to have a parameter with marker text "TODO: add a description here"
Create a Warning Recipe
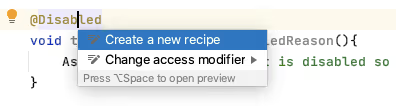
I use Alt+Enter to Create a new Recipe.
Then add the basic descriptive text in the general information.
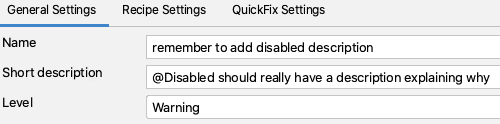
By making the rule a warning, any matching code is highlighted but not shown as a glaring error.
Find the Annotation
In the recipe editor, I change the Search to match an annotation.
This will highlight all annotations in the preview.
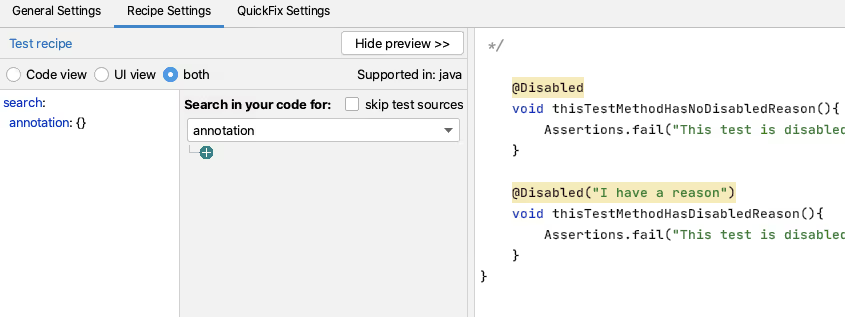
Having done that, I want to filter on the type of annotation.
I could just use Disabled but I fully qualify the class with the package so that it only matches the annotation from JUnit 5. Because the source code is shown in the preview, I can easily copy and paste this in from the actual code to avoid any typos.
I then want to match only annotations without Parameters, and I can use the GUI to do that.

i.e. Search:
search:
annotation:
type: "org.junit.jupiter.api.Disabled"
without:
parameters:
- {}
Create a Rewrite Quick Fix Action
For my QuickFix I will use a rewrite action.
I use the Show Variables functionality to show me the Mustache variables and preview the contents.
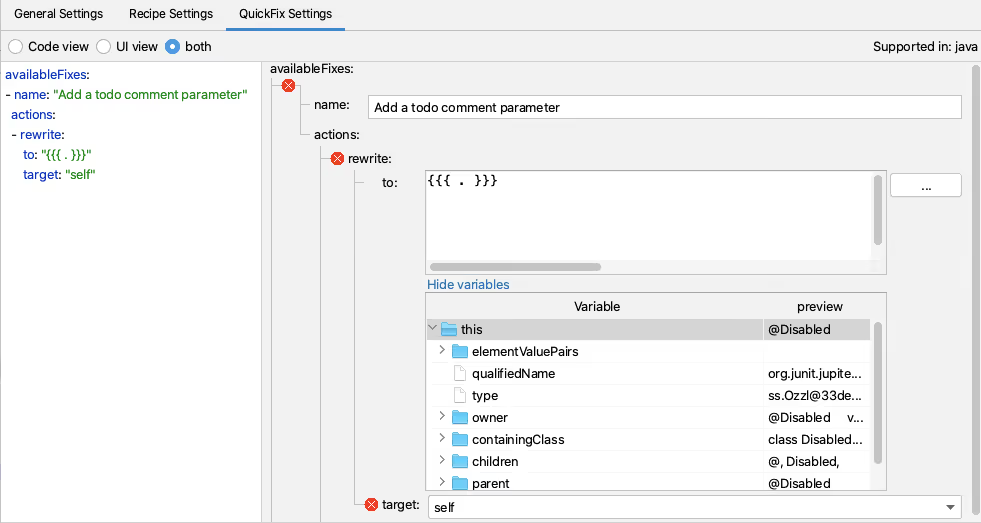
And then I add the extra code needed to create the place marker comment.

i.e. QuickFix:
availableFixes:
- name: "Add a todo comment parameter"
actions:
- rewrite:
to: "{{{ . }}}(\"TODO: add a description here\")"
target: "self"
Sensei in Action
We have created a short video showing the recipe creation process in action.
Summary
When building a rewrite Quick Fix, it is easier when we can search for the code element that we want to rewrite, because it is then the self entity we can act on.
In this example, I used a rewrite action to amend the Annotation. Rewrite is a general-purpose action that can apply to any code element and is a good default to explore.
Govern AI-driven development before it ships
Measure AI-assisted risk, enforce secure coding policy at commit, and accelerate secure delivery across your SDLC.
Explore more blogs
우리는 이 방법을 잘 알고 있습니다. 우리는 이 두 가지 축복을 골고루 살기 위해 노력하고 있습니다.

Security as culture: How Blue Prism cultivates world-class secure developers
Learn how Blue Prism, the global leader in intelligent automation for the enterprise, used Secure Code Warrior's agile learning platform to create a security-first culture with their developers, achieve their business goals, and ship secure code at speed

One Culture of Security: How Sage built their security champions program with agile secure code learning
Discover how Sage enhanced security with a flexible, relationship-focused approach, creating 200+ security champions and achieving measurable risk reduction.
Observe and Secure the ADLC: A Four-Point Framework for CISOs and Development Teams Using AI
While development teams look to make the most of GenAI’s undeniable benefits, we’d like to propose a four-point foundational framework that will allow security leaders to deploy AI coding tools and agents with a higher, more relevant standard of security best practices. It details exactly what enterprises can do to ensure safe, secure code development right now, and as agentic AI becomes an even bigger factor in the future.
Secure AI-driven development before it ships
See developer risk, enforce policy, and prevent vulnerabilities across your software development lifecycle.

%252520%252520(3).avif)

