
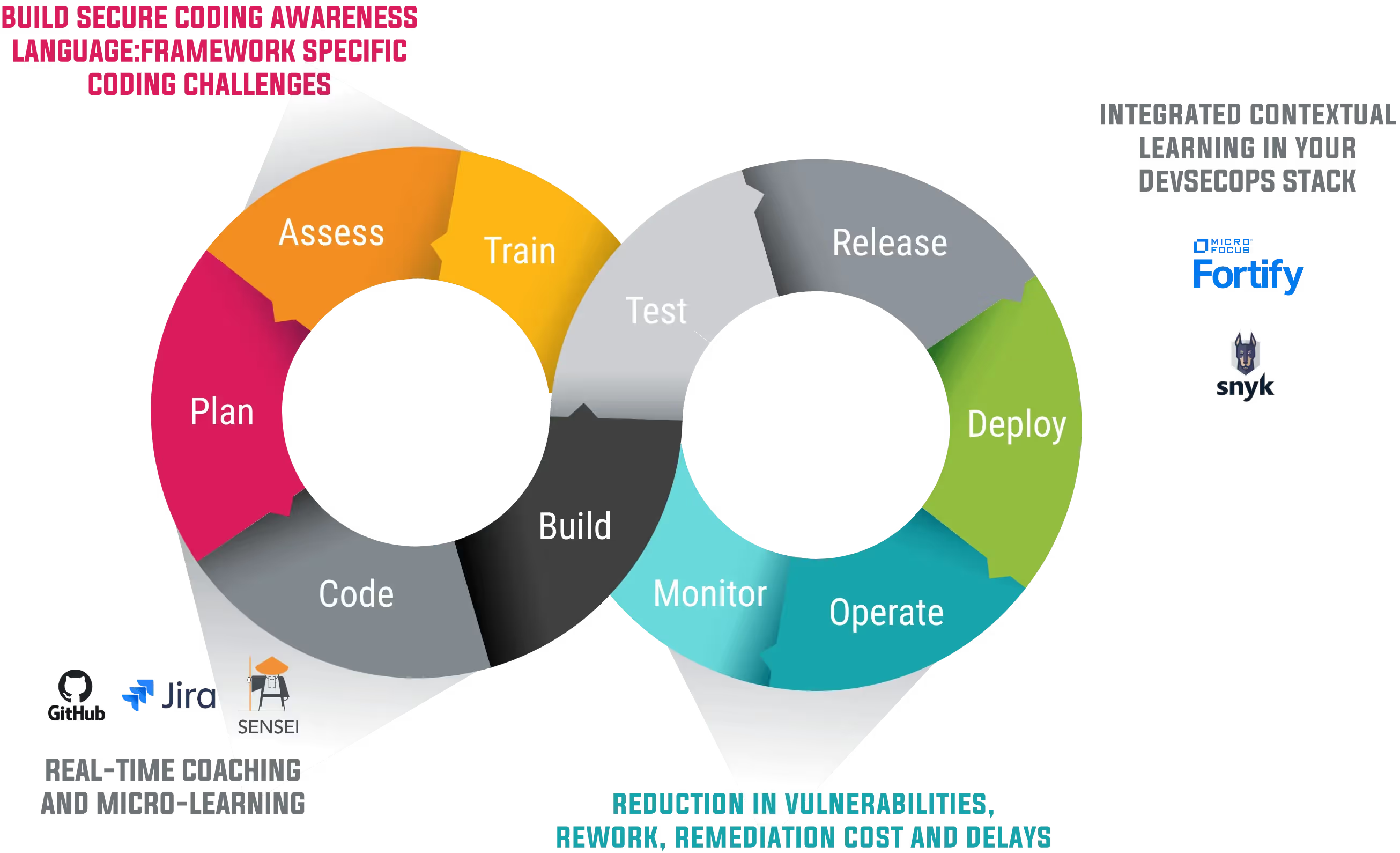
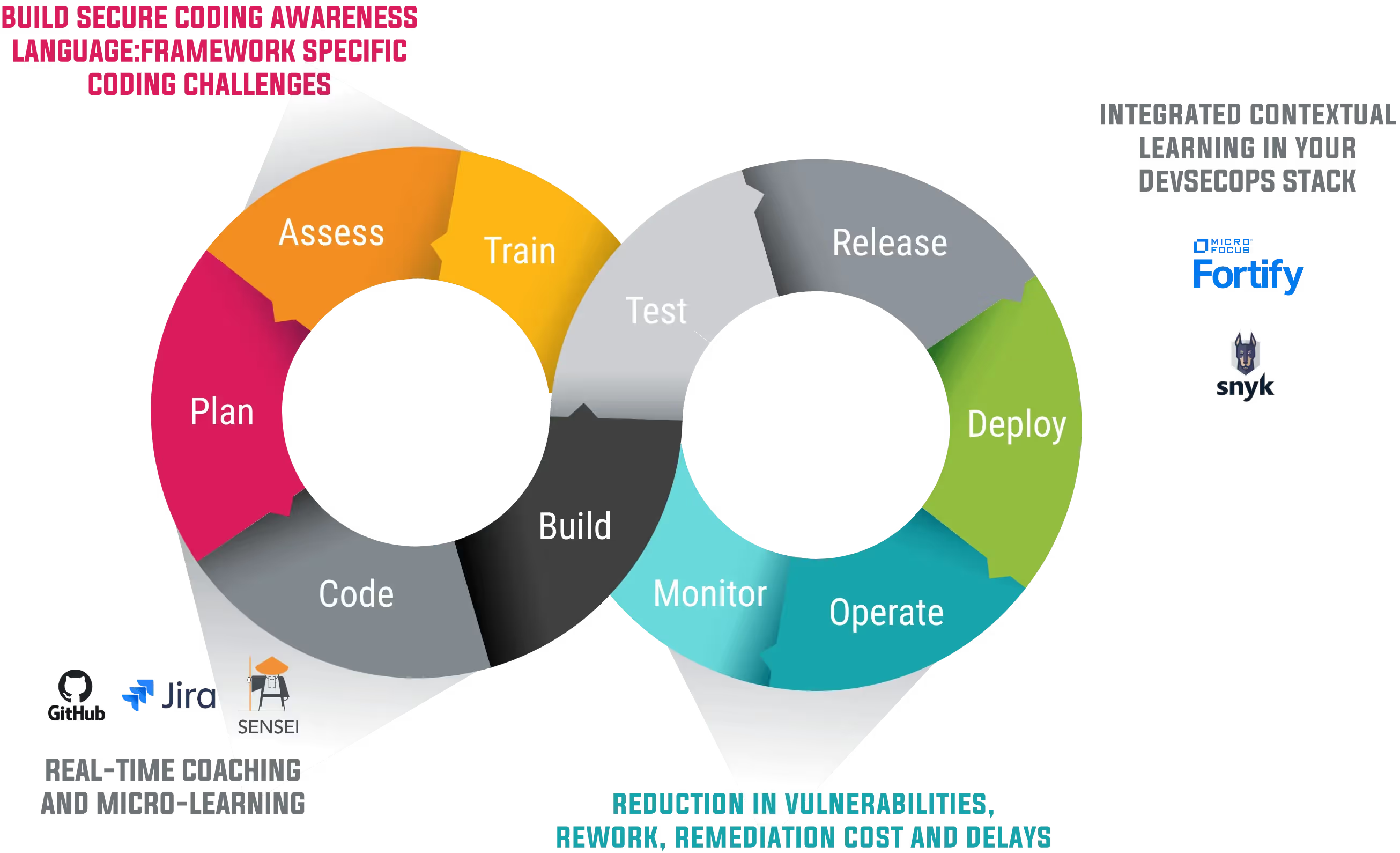
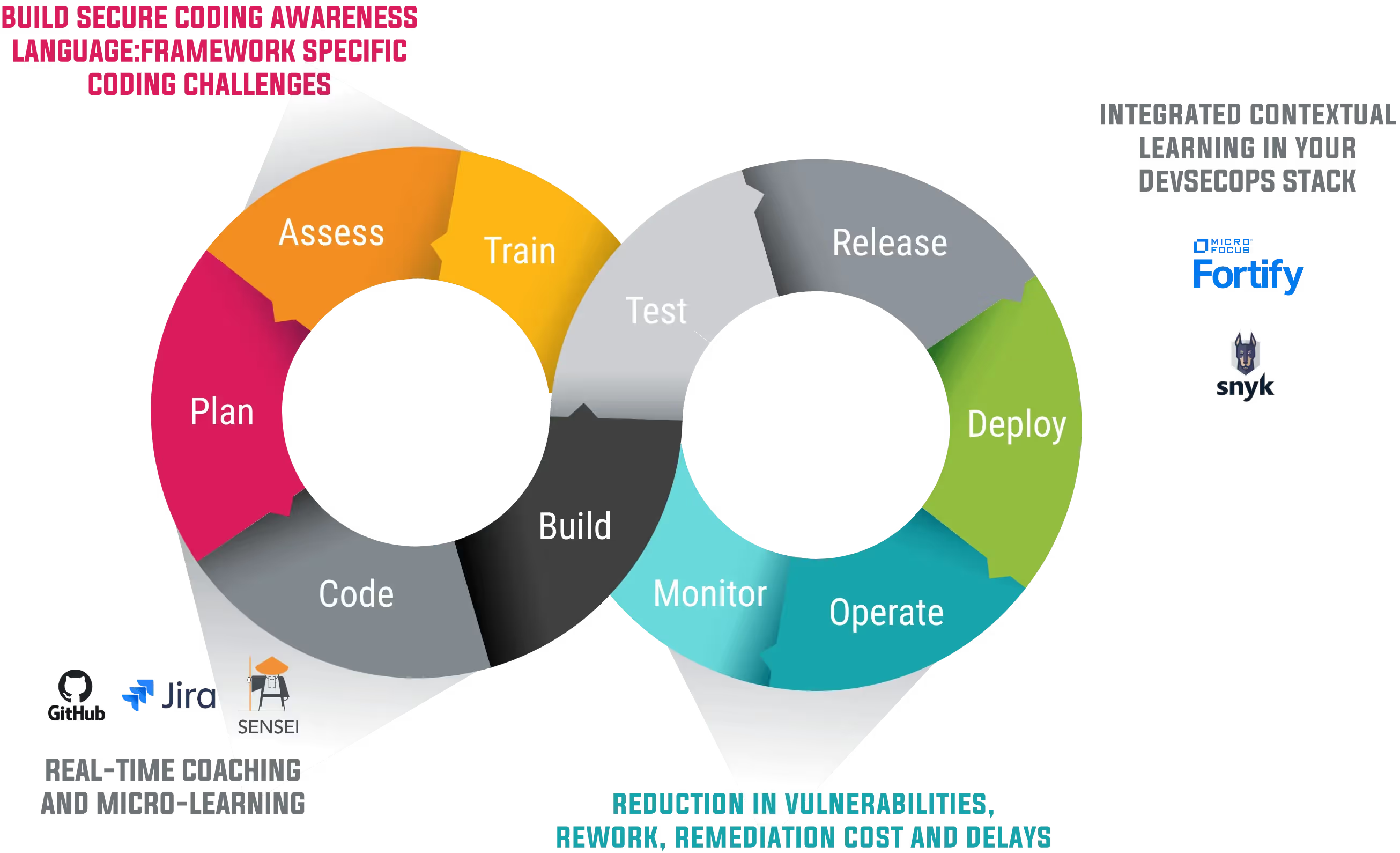
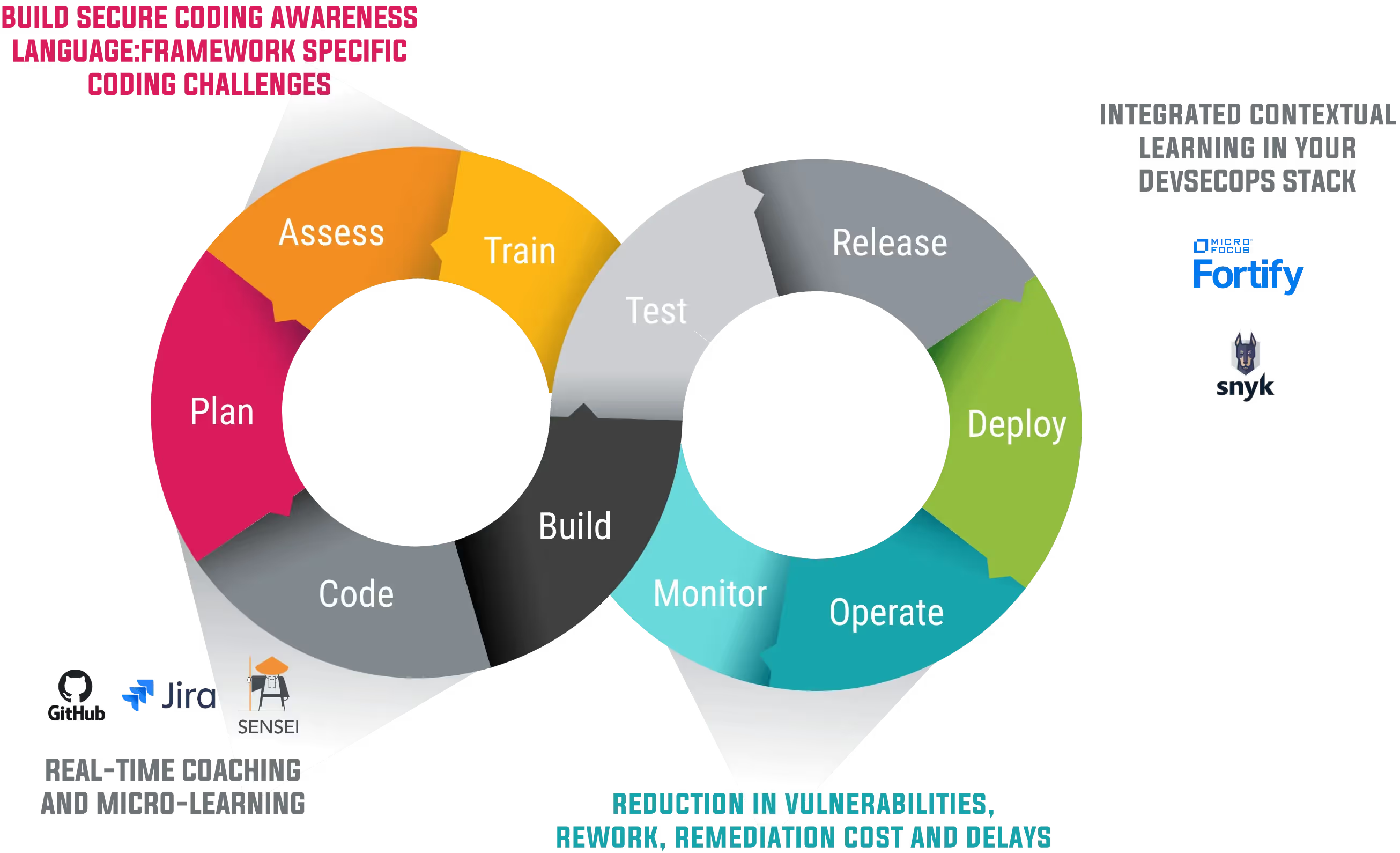
Développez des compétences de codage sécurisé à chaque étape du SSDLC
Add developer-centric training to industry-standard SARIF files, directly in GitHub code scanning workflows with our new GitHub Action.
On September 30th, GitHub officially announced the general availability of GitHub code scanning. GitHub code scanning is a developer-first, GitHub-native approach to easily finding security vulnerabilities before they reach production.
Code scanning integrates with GitHub Actions " or an existing CI/CD environment " to maximize flexibility for development teams. It scans code as it's created, surfacing actionable security reviews within pull requests, and automating security as a part of a GitHub workflow.
A seamless approach to security for developers.
Built on the open SARIF (Static Analysis Results Interchange Format) standard, code scanning is designed to flex with the ever-growing needs of organization, so they can include things like open-source and commercial static application security testing (SAST) solutions within the same GitHub-native experience.
Third-party code scanning tools can be initiated with a GitHub Action or a GitHub App based on an event in GitHub itself, like a pull request. The results are formatted as SARIF and uploaded to the GitHub Security Alerts tab. Alerts are then aggregated per tool, and GitHub can track and suppress duplicate alerts. This allows developers to use their tool of choice for any of their projects on GitHub, all within the native GitHub experience. Quite simply, it cuts through the disruption of some traditional approaches to security, and it respects the developer workflow.
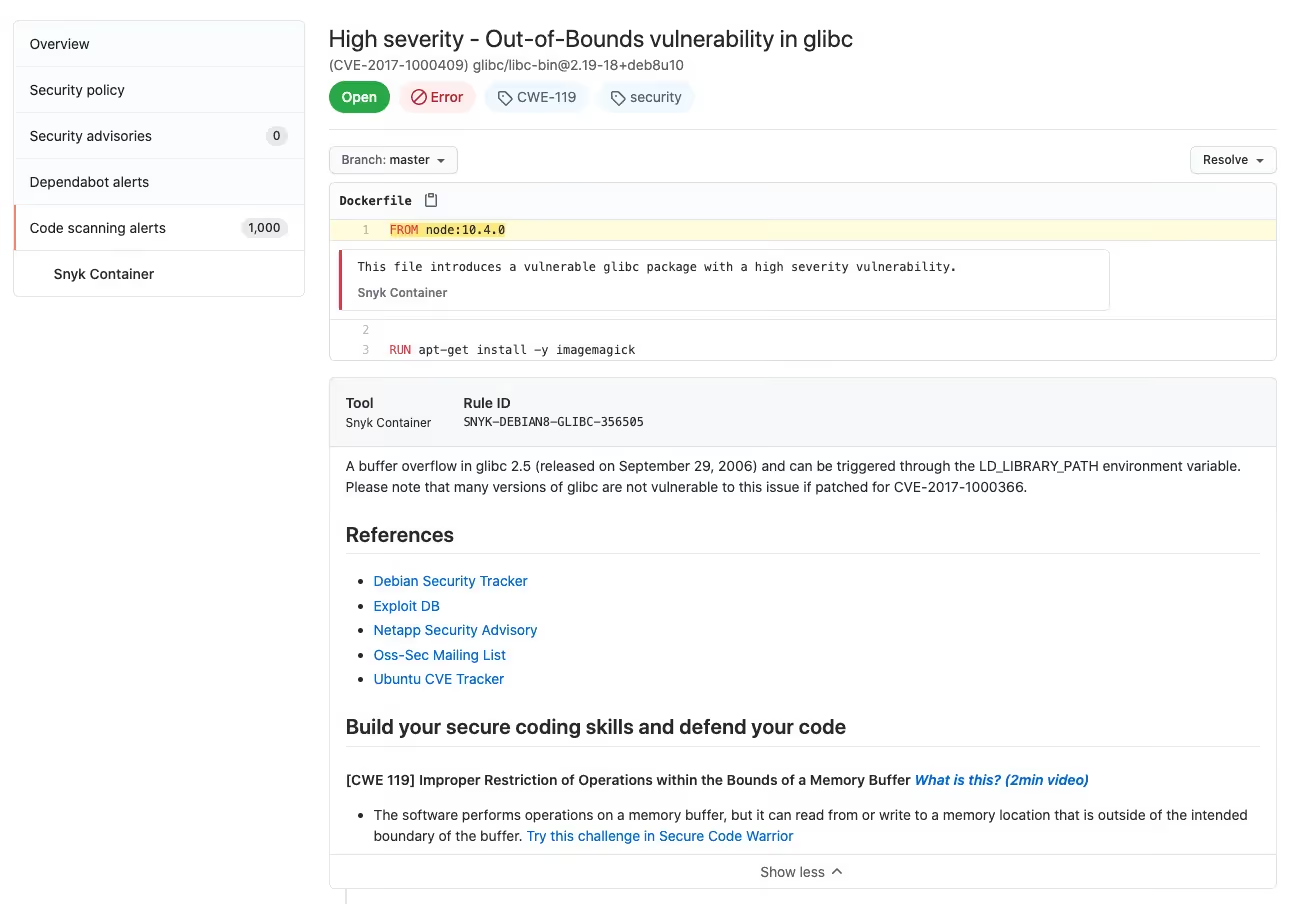
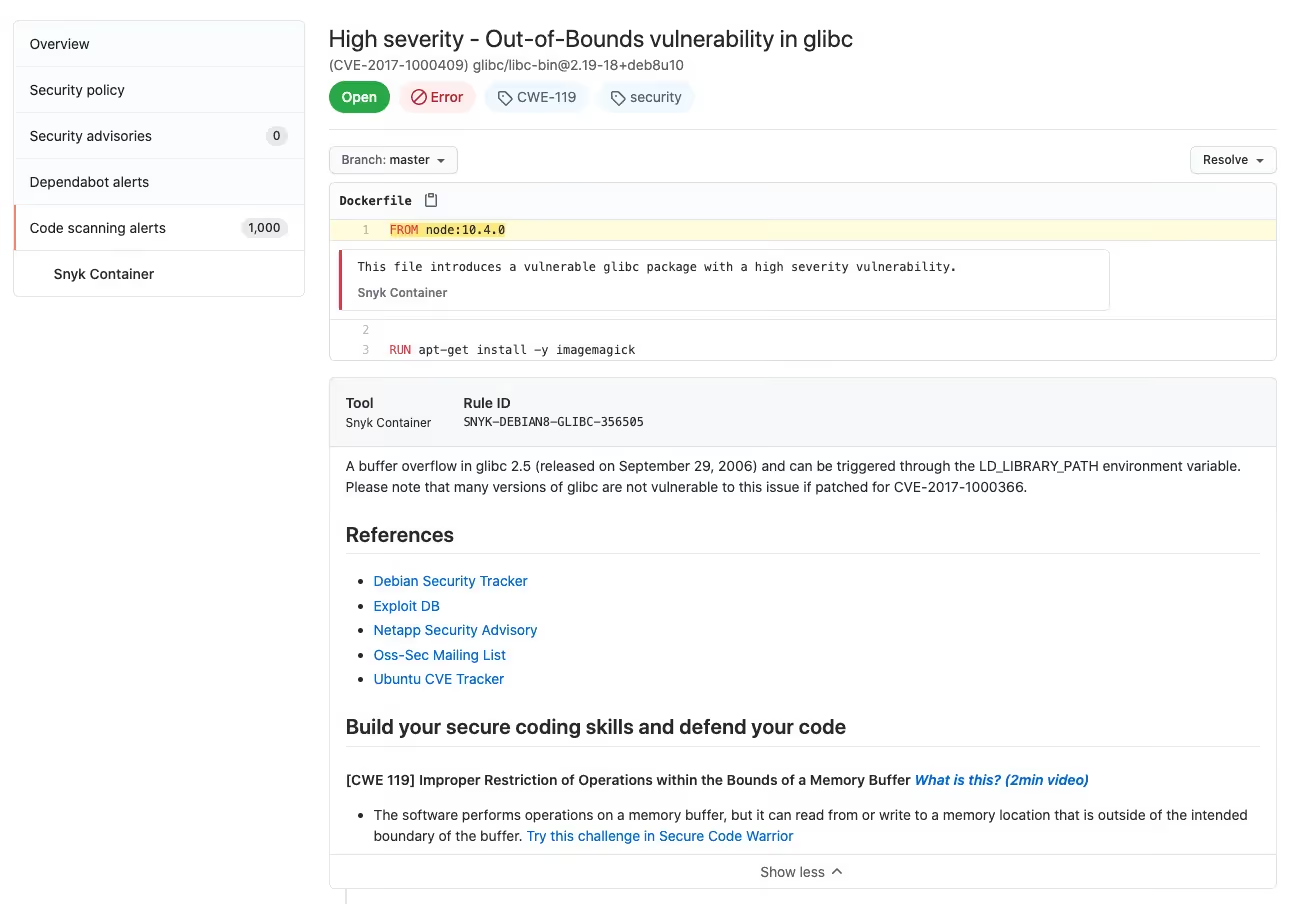
Yesterday, Secure Code Warrior was featured by GitHub as the only developer-centric training provider in their blog post, Third-Party Code Scanning Tools: Static Analysis & Developer Security Training, alongside Synk, Checkmarx, Fortify On Demand, Synopsis and Veracode.
While many SCA/SAST solutions provide lots of details for each of the vulnerabilities discovered, and references to published advisories and associated CWEs, not every developer is a security expert, nor should that be expected of them. Practical, usable advice and tools are the key to actionable awareness.
Contextual micro-learning.
The more context developers have for vulnerabilities, the more they're able to understand the risks, prioritize fixing the most pressing issues and ultimately prevent them in the first place. That's where Secure Code Warrior comes in. Our mission is to empower developers to write secure code from the very beginning through fun, engaging, and framework-specific training, helping them think and code with a security mindset to achieve rapid improvements in security compliance, consistency, quality and development speed.
GitHub code scanning integration
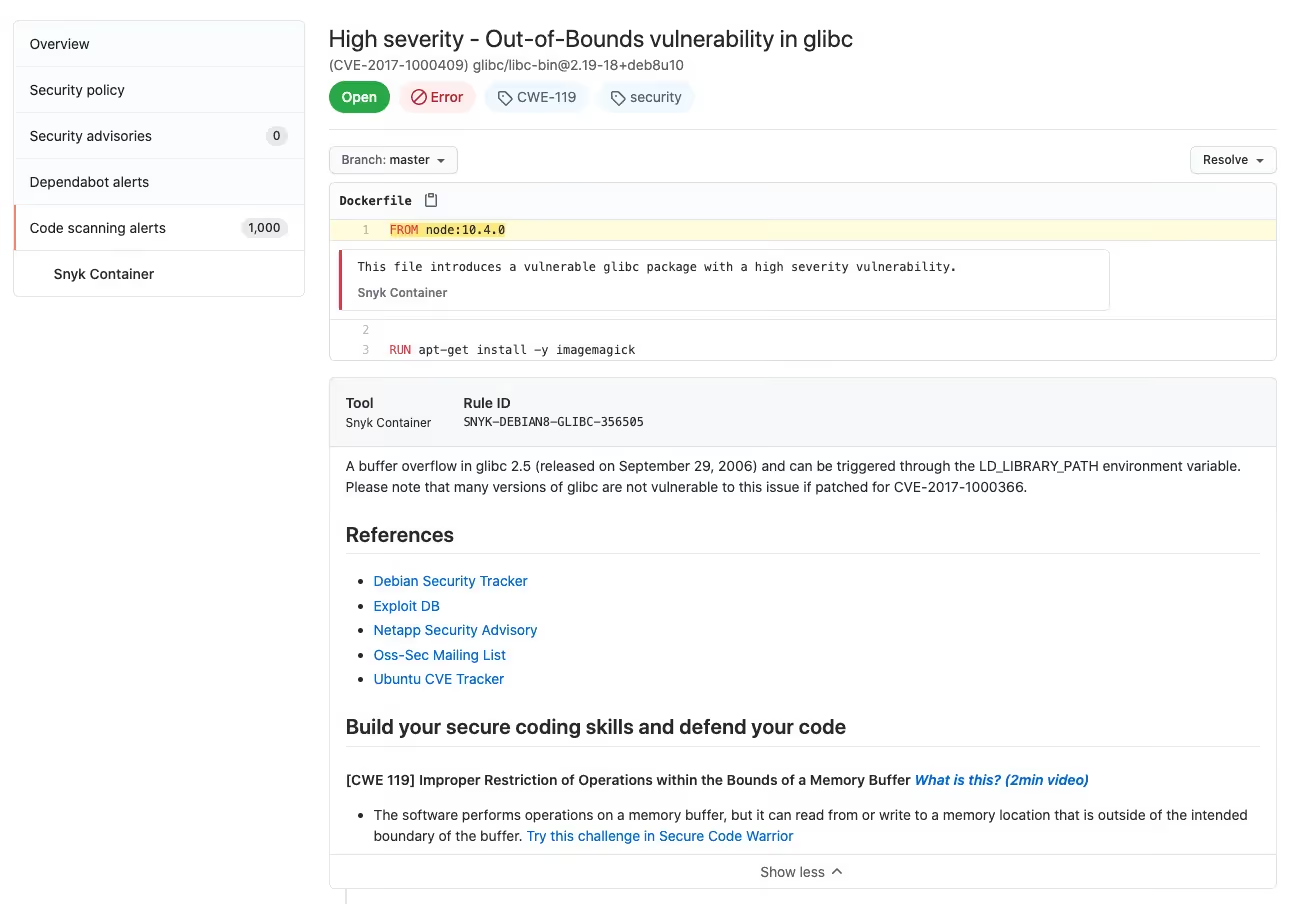
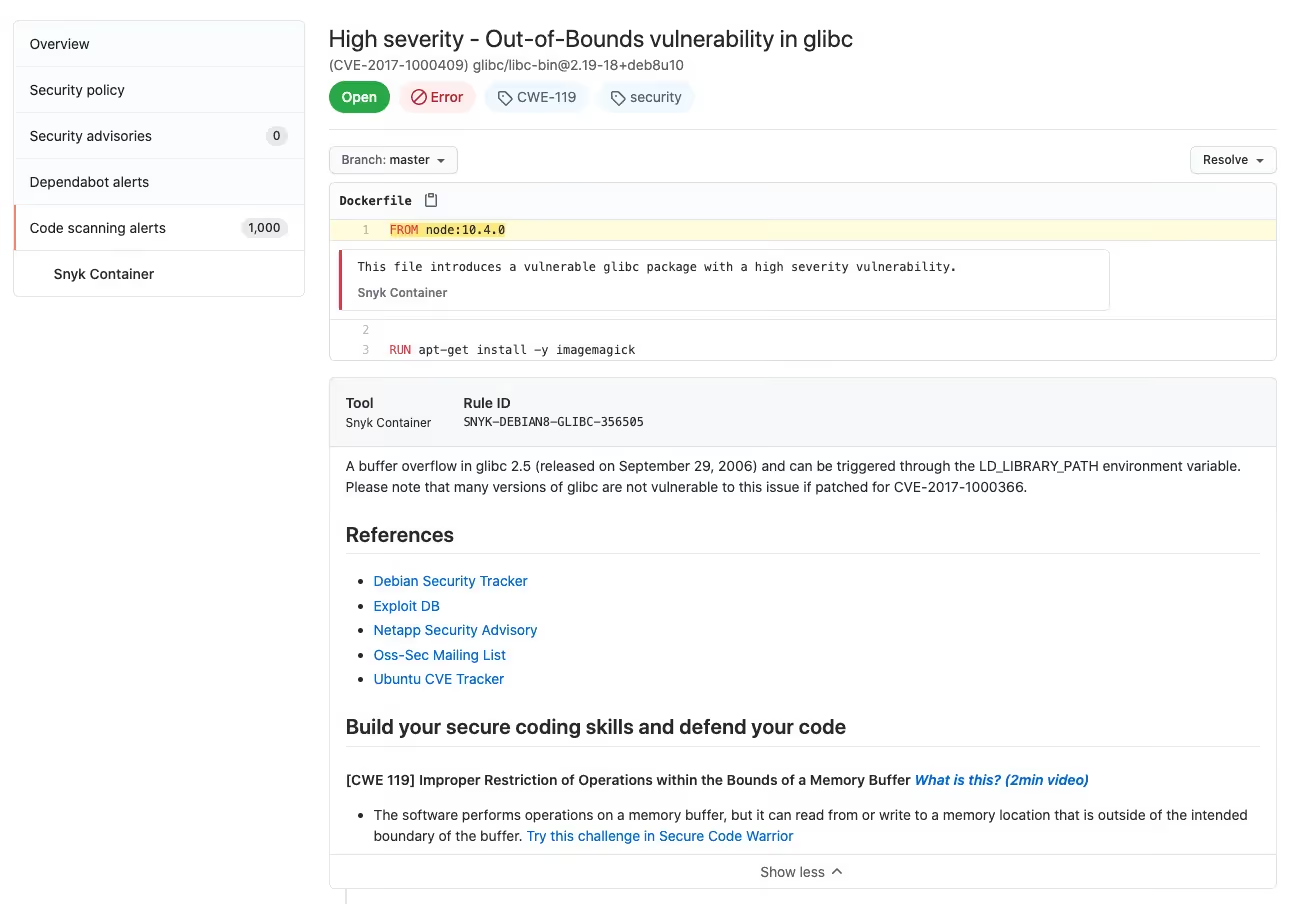
Secure Code Warrior has built a GitHub Action that brings contextual learning to GitHub code scanning. This means developers can use a third-party action like the Snyk Container Action to find vulnerabilities, and then augment the output with CWE-specific, hyper-relevant learning.
The Secure Code Warrior GitHub Action processes an industry-standard SARIF file and appends contextual learning based upon CWE references in a SARIF rule object. This empowers development and security teams to not only find vulnerabilities, but enrich supported SAST tool reports with actionable knowledge that helps them prevent vulnerabilities from reoccurring.
Ready to try it out for yourself?
Get the action for free directly from the GitHub Marketplace here.
Learn more about the Secure Code Warrior GitHub Action here.


Secure Code Warrior a créé une action GitHub qui intègre l'apprentissage contextuel à l'analyse du code GitHub. Cela signifie que les développeurs peuvent utiliser une action tierce telle que l'action Snyk Container pour détecter les vulnérabilités, puis augmenter le résultat avec un apprentissage hyperpertinent et spécifique à CWE.
Matias Madou, Ph.D. est expert en sécurité, chercheur, directeur technique et cofondateur de Secure Code Warrior. Matias a obtenu son doctorat en sécurité des applications à l'université de Gand, en se concentrant sur les solutions d'analyse statique. Il a ensuite rejoint Fortify aux États-Unis, où il s'est rendu compte qu'il ne suffisait pas de détecter uniquement les problèmes de code sans aider les développeurs à écrire du code sécurisé. Cela l'a incité à développer des produits qui aident les développeurs, allègent le fardeau de la sécurité et dépassent les attentes des clients. Lorsqu'il n'est pas à son bureau au sein de Team Awesome, il aime être sur scène pour faire des présentations lors de conférences telles que RSA Conference, BlackHat et DefCon.

Secure Code Warrior est là pour aider votre organisation à sécuriser le code tout au long du cycle de développement logiciel et à créer une culture dans laquelle la cybersécurité est une priorité. Que vous soyez responsable de la sécurité des applications, développeur, responsable de la sécurité informatique ou toute autre personne impliquée dans la sécurité, nous pouvons aider votre organisation à réduire les risques associés à un code non sécurisé.
Réservez une démoMatias Madou, Ph.D. est expert en sécurité, chercheur, directeur technique et cofondateur de Secure Code Warrior. Matias a obtenu son doctorat en sécurité des applications à l'université de Gand, en se concentrant sur les solutions d'analyse statique. Il a ensuite rejoint Fortify aux États-Unis, où il s'est rendu compte qu'il ne suffisait pas de détecter uniquement les problèmes de code sans aider les développeurs à écrire du code sécurisé. Cela l'a incité à développer des produits qui aident les développeurs, allègent le fardeau de la sécurité et dépassent les attentes des clients. Lorsqu'il n'est pas à son bureau au sein de Team Awesome, il aime être sur scène pour faire des présentations lors de conférences telles que RSA Conference, BlackHat et DefCon.
Matias est un chercheur et développeur qui possède plus de 15 ans d'expérience pratique en matière de sécurité logicielle. Il a développé des solutions pour des entreprises telles que Fortify Software et sa propre société Sensei Security. Au cours de sa carrière, Matias a dirigé de nombreux projets de recherche sur la sécurité des applications qui ont abouti à des produits commerciaux et possède plus de 10 brevets à son actif. Lorsqu'il n'est pas à son bureau, Matias a enseigné des cours de formation avancée sur la sécurité des applications et prend régulièrement la parole lors de conférences mondiales telles que RSA Conference, Black Hat, DefCon, BSIMM, OWASP AppSec et BruCon.
Matias est titulaire d'un doctorat en génie informatique de l'université de Gand, où il a étudié la sécurité des applications par le biais de l'obfuscation de programmes pour masquer le fonctionnement interne d'une application.


Add developer-centric training to industry-standard SARIF files, directly in GitHub code scanning workflows with our new GitHub Action.
On September 30th, GitHub officially announced the general availability of GitHub code scanning. GitHub code scanning is a developer-first, GitHub-native approach to easily finding security vulnerabilities before they reach production.
Code scanning integrates with GitHub Actions " or an existing CI/CD environment " to maximize flexibility for development teams. It scans code as it's created, surfacing actionable security reviews within pull requests, and automating security as a part of a GitHub workflow.
A seamless approach to security for developers.
Built on the open SARIF (Static Analysis Results Interchange Format) standard, code scanning is designed to flex with the ever-growing needs of organization, so they can include things like open-source and commercial static application security testing (SAST) solutions within the same GitHub-native experience.
Third-party code scanning tools can be initiated with a GitHub Action or a GitHub App based on an event in GitHub itself, like a pull request. The results are formatted as SARIF and uploaded to the GitHub Security Alerts tab. Alerts are then aggregated per tool, and GitHub can track and suppress duplicate alerts. This allows developers to use their tool of choice for any of their projects on GitHub, all within the native GitHub experience. Quite simply, it cuts through the disruption of some traditional approaches to security, and it respects the developer workflow.
Yesterday, Secure Code Warrior was featured by GitHub as the only developer-centric training provider in their blog post, Third-Party Code Scanning Tools: Static Analysis & Developer Security Training, alongside Synk, Checkmarx, Fortify On Demand, Synopsis and Veracode.
While many SCA/SAST solutions provide lots of details for each of the vulnerabilities discovered, and references to published advisories and associated CWEs, not every developer is a security expert, nor should that be expected of them. Practical, usable advice and tools are the key to actionable awareness.
Contextual micro-learning.
The more context developers have for vulnerabilities, the more they're able to understand the risks, prioritize fixing the most pressing issues and ultimately prevent them in the first place. That's where Secure Code Warrior comes in. Our mission is to empower developers to write secure code from the very beginning through fun, engaging, and framework-specific training, helping them think and code with a security mindset to achieve rapid improvements in security compliance, consistency, quality and development speed.
GitHub code scanning integration
Secure Code Warrior has built a GitHub Action that brings contextual learning to GitHub code scanning. This means developers can use a third-party action like the Snyk Container Action to find vulnerabilities, and then augment the output with CWE-specific, hyper-relevant learning.
The Secure Code Warrior GitHub Action processes an industry-standard SARIF file and appends contextual learning based upon CWE references in a SARIF rule object. This empowers development and security teams to not only find vulnerabilities, but enrich supported SAST tool reports with actionable knowledge that helps them prevent vulnerabilities from reoccurring.
Ready to try it out for yourself?
Get the action for free directly from the GitHub Marketplace here.
Learn more about the Secure Code Warrior GitHub Action here.

Add developer-centric training to industry-standard SARIF files, directly in GitHub code scanning workflows with our new GitHub Action.
On September 30th, GitHub officially announced the general availability of GitHub code scanning. GitHub code scanning is a developer-first, GitHub-native approach to easily finding security vulnerabilities before they reach production.
Code scanning integrates with GitHub Actions " or an existing CI/CD environment " to maximize flexibility for development teams. It scans code as it's created, surfacing actionable security reviews within pull requests, and automating security as a part of a GitHub workflow.
A seamless approach to security for developers.
Built on the open SARIF (Static Analysis Results Interchange Format) standard, code scanning is designed to flex with the ever-growing needs of organization, so they can include things like open-source and commercial static application security testing (SAST) solutions within the same GitHub-native experience.
Third-party code scanning tools can be initiated with a GitHub Action or a GitHub App based on an event in GitHub itself, like a pull request. The results are formatted as SARIF and uploaded to the GitHub Security Alerts tab. Alerts are then aggregated per tool, and GitHub can track and suppress duplicate alerts. This allows developers to use their tool of choice for any of their projects on GitHub, all within the native GitHub experience. Quite simply, it cuts through the disruption of some traditional approaches to security, and it respects the developer workflow.
Yesterday, Secure Code Warrior was featured by GitHub as the only developer-centric training provider in their blog post, Third-Party Code Scanning Tools: Static Analysis & Developer Security Training, alongside Synk, Checkmarx, Fortify On Demand, Synopsis and Veracode.
While many SCA/SAST solutions provide lots of details for each of the vulnerabilities discovered, and references to published advisories and associated CWEs, not every developer is a security expert, nor should that be expected of them. Practical, usable advice and tools are the key to actionable awareness.
Contextual micro-learning.
The more context developers have for vulnerabilities, the more they're able to understand the risks, prioritize fixing the most pressing issues and ultimately prevent them in the first place. That's where Secure Code Warrior comes in. Our mission is to empower developers to write secure code from the very beginning through fun, engaging, and framework-specific training, helping them think and code with a security mindset to achieve rapid improvements in security compliance, consistency, quality and development speed.
GitHub code scanning integration
Secure Code Warrior has built a GitHub Action that brings contextual learning to GitHub code scanning. This means developers can use a third-party action like the Snyk Container Action to find vulnerabilities, and then augment the output with CWE-specific, hyper-relevant learning.
The Secure Code Warrior GitHub Action processes an industry-standard SARIF file and appends contextual learning based upon CWE references in a SARIF rule object. This empowers development and security teams to not only find vulnerabilities, but enrich supported SAST tool reports with actionable knowledge that helps them prevent vulnerabilities from reoccurring.
Ready to try it out for yourself?
Get the action for free directly from the GitHub Marketplace here.
Learn more about the Secure Code Warrior GitHub Action here.

Cliquez sur le lien ci-dessous et téléchargez le PDF de cette ressource.
Secure Code Warrior est là pour aider votre organisation à sécuriser le code tout au long du cycle de développement logiciel et à créer une culture dans laquelle la cybersécurité est une priorité. Que vous soyez responsable de la sécurité des applications, développeur, responsable de la sécurité informatique ou toute autre personne impliquée dans la sécurité, nous pouvons aider votre organisation à réduire les risques associés à un code non sécurisé.
Afficher le rapportRéservez une démoMatias Madou, Ph.D. est expert en sécurité, chercheur, directeur technique et cofondateur de Secure Code Warrior. Matias a obtenu son doctorat en sécurité des applications à l'université de Gand, en se concentrant sur les solutions d'analyse statique. Il a ensuite rejoint Fortify aux États-Unis, où il s'est rendu compte qu'il ne suffisait pas de détecter uniquement les problèmes de code sans aider les développeurs à écrire du code sécurisé. Cela l'a incité à développer des produits qui aident les développeurs, allègent le fardeau de la sécurité et dépassent les attentes des clients. Lorsqu'il n'est pas à son bureau au sein de Team Awesome, il aime être sur scène pour faire des présentations lors de conférences telles que RSA Conference, BlackHat et DefCon.
Matias est un chercheur et développeur qui possède plus de 15 ans d'expérience pratique en matière de sécurité logicielle. Il a développé des solutions pour des entreprises telles que Fortify Software et sa propre société Sensei Security. Au cours de sa carrière, Matias a dirigé de nombreux projets de recherche sur la sécurité des applications qui ont abouti à des produits commerciaux et possède plus de 10 brevets à son actif. Lorsqu'il n'est pas à son bureau, Matias a enseigné des cours de formation avancée sur la sécurité des applications et prend régulièrement la parole lors de conférences mondiales telles que RSA Conference, Black Hat, DefCon, BSIMM, OWASP AppSec et BruCon.
Matias est titulaire d'un doctorat en génie informatique de l'université de Gand, où il a étudié la sécurité des applications par le biais de l'obfuscation de programmes pour masquer le fonctionnement interne d'une application.
Add developer-centric training to industry-standard SARIF files, directly in GitHub code scanning workflows with our new GitHub Action.
On September 30th, GitHub officially announced the general availability of GitHub code scanning. GitHub code scanning is a developer-first, GitHub-native approach to easily finding security vulnerabilities before they reach production.
Code scanning integrates with GitHub Actions " or an existing CI/CD environment " to maximize flexibility for development teams. It scans code as it's created, surfacing actionable security reviews within pull requests, and automating security as a part of a GitHub workflow.
A seamless approach to security for developers.
Built on the open SARIF (Static Analysis Results Interchange Format) standard, code scanning is designed to flex with the ever-growing needs of organization, so they can include things like open-source and commercial static application security testing (SAST) solutions within the same GitHub-native experience.
Third-party code scanning tools can be initiated with a GitHub Action or a GitHub App based on an event in GitHub itself, like a pull request. The results are formatted as SARIF and uploaded to the GitHub Security Alerts tab. Alerts are then aggregated per tool, and GitHub can track and suppress duplicate alerts. This allows developers to use their tool of choice for any of their projects on GitHub, all within the native GitHub experience. Quite simply, it cuts through the disruption of some traditional approaches to security, and it respects the developer workflow.
Yesterday, Secure Code Warrior was featured by GitHub as the only developer-centric training provider in their blog post, Third-Party Code Scanning Tools: Static Analysis & Developer Security Training, alongside Synk, Checkmarx, Fortify On Demand, Synopsis and Veracode.
While many SCA/SAST solutions provide lots of details for each of the vulnerabilities discovered, and references to published advisories and associated CWEs, not every developer is a security expert, nor should that be expected of them. Practical, usable advice and tools are the key to actionable awareness.
Contextual micro-learning.
The more context developers have for vulnerabilities, the more they're able to understand the risks, prioritize fixing the most pressing issues and ultimately prevent them in the first place. That's where Secure Code Warrior comes in. Our mission is to empower developers to write secure code from the very beginning through fun, engaging, and framework-specific training, helping them think and code with a security mindset to achieve rapid improvements in security compliance, consistency, quality and development speed.
GitHub code scanning integration
Secure Code Warrior has built a GitHub Action that brings contextual learning to GitHub code scanning. This means developers can use a third-party action like the Snyk Container Action to find vulnerabilities, and then augment the output with CWE-specific, hyper-relevant learning.
The Secure Code Warrior GitHub Action processes an industry-standard SARIF file and appends contextual learning based upon CWE references in a SARIF rule object. This empowers development and security teams to not only find vulnerabilities, but enrich supported SAST tool reports with actionable knowledge that helps them prevent vulnerabilities from reoccurring.
Ready to try it out for yourself?
Get the action for free directly from the GitHub Marketplace here.
Learn more about the Secure Code Warrior GitHub Action here.
Table des matières
Matias Madou, Ph.D. est expert en sécurité, chercheur, directeur technique et cofondateur de Secure Code Warrior. Matias a obtenu son doctorat en sécurité des applications à l'université de Gand, en se concentrant sur les solutions d'analyse statique. Il a ensuite rejoint Fortify aux États-Unis, où il s'est rendu compte qu'il ne suffisait pas de détecter uniquement les problèmes de code sans aider les développeurs à écrire du code sécurisé. Cela l'a incité à développer des produits qui aident les développeurs, allègent le fardeau de la sécurité et dépassent les attentes des clients. Lorsqu'il n'est pas à son bureau au sein de Team Awesome, il aime être sur scène pour faire des présentations lors de conférences telles que RSA Conference, BlackHat et DefCon.

Secure Code Warrior est là pour aider votre organisation à sécuriser le code tout au long du cycle de développement logiciel et à créer une culture dans laquelle la cybersécurité est une priorité. Que vous soyez responsable de la sécurité des applications, développeur, responsable de la sécurité informatique ou toute autre personne impliquée dans la sécurité, nous pouvons aider votre organisation à réduire les risques associés à un code non sécurisé.
Réservez une démoTéléchargerRessources pour vous aider à démarrer
Ressources pour vous aider à démarrer
Secure Code Warrior named twice in the Gartner Hype Cycle for secure software engineering
Gartner names SCW twice. As AI agents take over more development, SCW gives you the capability and governance to adopt AI-driven development securely.
Secure coding learning that reflects real AI usage
Align secure coding training to real AI development activity — automatically assigning guidance to developers using AI tools, without manual intervention.Align secure coding training to real AI development activity — automatically assigning guidance to developers using AI tools, without manual intervention.
Train developers on the real risks in their code, whether human-written or AI-generated
Adaptive Learning auto-assigns targeted secure coding training to the developers introducing real vulnerabilities, reducing recurring risks at the source.Secure Code Warrior blog banner with a blue overlay over a developer working at a multi-monitor desk displaying code, alongside the headline 'Train developers on the real risks in their code.'l















