
私のワークフローを混乱させるのはやめましょう!適切なセキュリティトレーニングを適切なタイミングで受ける方法
Think about the last time you were at work, perhaps in a software project team working to an impossible deadline. And then, your manager comes along and says there is some mandatory security training to do, and that it needs to be shoehorned into your workday on top of everything else.
They know it, and you know it. It's a huge PITA, but for compliance reasons, you'll be playing some boring training videos in the background while you keep coding, tuning in and out of both tasks and giving your full attention to neither. This is a common scenario; it's highly disruptive, and it wastes everyone's time. Most security training is too generic, and it's easy to ignore something that bounces in and out of a workday with no real value.
As a company, our goal is to bring a better, more effective type of security training to you, and this is born from knowing exactly what it's like to be disengaged from what the AppSec team tells you is important, when each of your priorities is misaligned. What is interesting, though, is that we started to think about what we could do to reduce the barrier to getting training when you need it - even with our full platform, there are a few steps involved that take you away from your work, at moments where you still need a helpful push but can't dedicate a block of concentration to a training session.
We looked at how micro-learning could be implemented into your workflow, in the IDE or issue tracker, in a more seamless way. And this is what we came up with:
This is based on Just-in-Time (JiT) principles, wherein you're served the right knowledge, at the right time for it to be immediately effective and useful. It's the opposite of the just in case approach to learning, which is often a state of information overload that takes away precious time and headspace for building features.
Quality code is secure code, and if you need a non-invasive security sidekick to collaborate with occasionally, then it might be worth your while to take it for a test drive.
Eliminate the barriers, and bring the training to you.
Cybersecurity might be an interest for some, but not everyone. And no-one should expect developers to become security experts - that still remains the job of specialist AppSec teams. However, security-aware developers are revered for their skills, and the protection they can offer organizations right from the code-building stage. It's a position in high demand, and you can build the foundations over time with contextual micro-learning.
Now, if you're thinking about integrated training as more like Clippy (may he rest in peace), then it's important to note that in the case of Secure Code Warrior's integrations, they're built by developers for developers, so the irritation factor has been considered and obliterated.
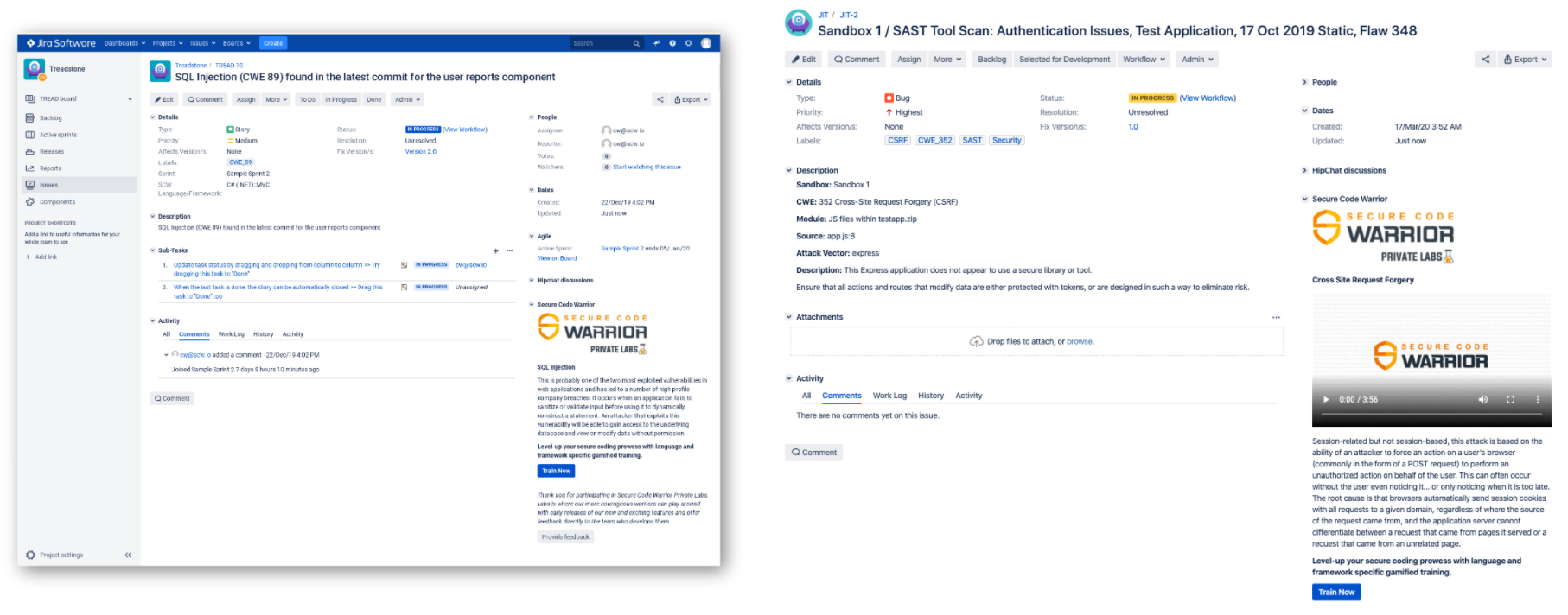
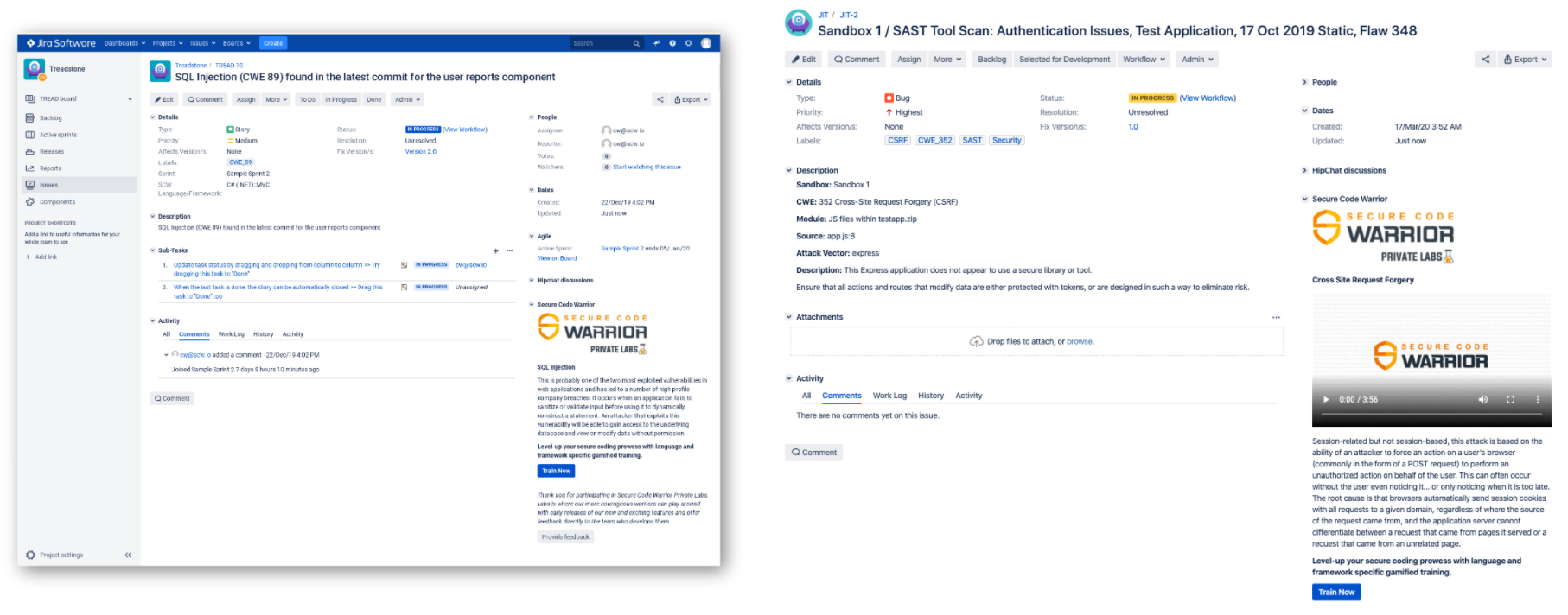
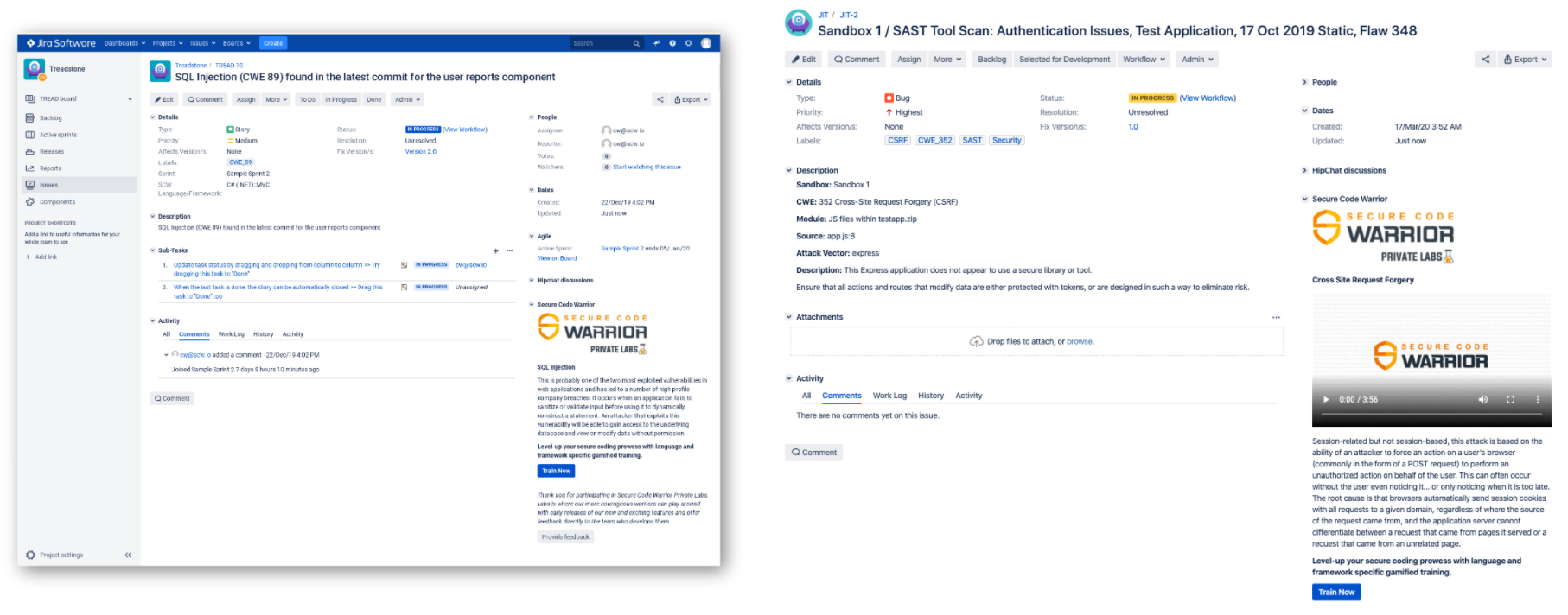
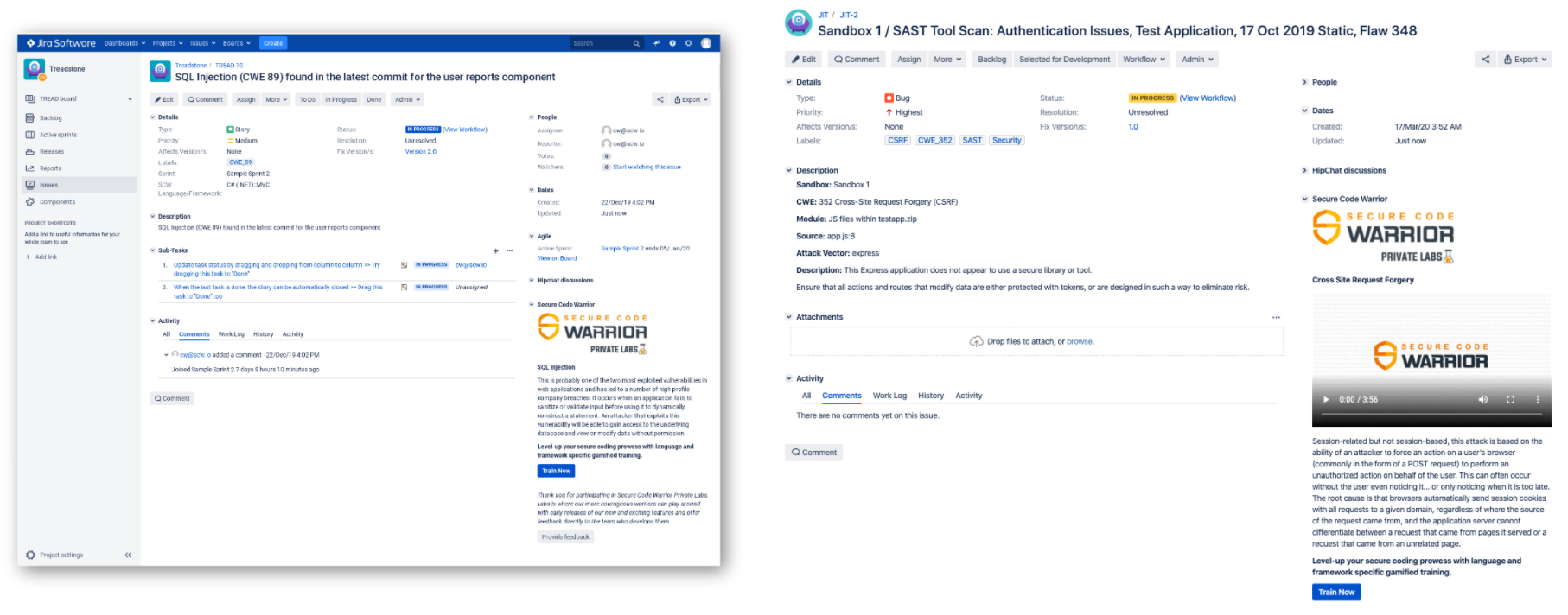
Let's check it out in action:

Secure Code Warrior for Github inspects code for Common Weakness Enumeration (CWE) or OWASP references in the labels, issue title, and body of issues to display contextual just-in-time training. The way it works is if a vulnerability reference is found, a comment will be posted on the issue to assist in swift resolution and prevention of recurring vulnerabilities. It integrates with the issue without disruption of your process, or making you jump through hoops for a solution.
And if you use Jira, the process is similar:

Now, for the incumbent security-aware superstars, it's important to remember that it's not all on you to make magic happen. You're going to need support, training, and a reason to take security seriously and get it into your own workflow. Luckily, this is all part of a functioning DevSecOps process, and lots of organizations are already taking note. Why not get a head start?
Download them now, and let us know what you think.
マティアス・マドゥ博士は、セキュリティ専門家、研究者、CTO、セキュア・コード・ウォリアーの共同創設者です。Matias はゲント大学で静的分析ソリューションを中心にアプリケーションセキュリティの博士号を取得しました。その後、米国のFortifyに入社し、開発者が安全なコードを書くのを手伝わずに、コードの問題を検出するだけでは不十分であることに気づきました。これがきっかけで、開発者を支援し、セキュリティの負担を軽減し、顧客の期待を超える製品を開発するようになりました。Team Awesome の一員としてデスクにいないときは、RSA カンファレンス、BlackHat、DefCon などのカンファレンスでプレゼンテーションを行うステージでのプレゼンテーションを楽しんでいます。

Secure Code Warriorは、ソフトウェア開発ライフサイクル全体にわたってコードを保護し、サイバーセキュリティを最優先とする文化を築くお手伝いをします。アプリケーションセキュリティマネージャ、開発者、CISO、またはセキュリティ関係者のいずれであっても、安全でないコードに関連するリスクを軽減するお手伝いをします。
デモを予約マティアス・マドゥ博士は、セキュリティ専門家、研究者、CTO、セキュア・コード・ウォリアーの共同創設者です。Matias はゲント大学で静的分析ソリューションを中心にアプリケーションセキュリティの博士号を取得しました。その後、米国のFortifyに入社し、開発者が安全なコードを書くのを手伝わずに、コードの問題を検出するだけでは不十分であることに気づきました。これがきっかけで、開発者を支援し、セキュリティの負担を軽減し、顧客の期待を超える製品を開発するようになりました。Team Awesome の一員としてデスクにいないときは、RSA カンファレンス、BlackHat、DefCon などのカンファレンスでプレゼンテーションを行うステージでのプレゼンテーションを楽しんでいます。
Matiasは、15年以上のソフトウェアセキュリティの実務経験を持つ研究者および開発者です。フォーティファイ・ソフトウェアや自身の会社であるセンセイ・セキュリティなどの企業向けにソリューションを開発してきました。マティアスはキャリアを通じて、複数のアプリケーションセキュリティ研究プロジェクトを主導し、それが商用製品につながり、10件以上の特許を取得しています。デスクから離れているときには、マティアスは上級アプリケーション・セキュリティ・トレーニング・コースの講師を務め、RSA Conference、Black Hat、DefCon、BSIMM、OWASP AppSec、BruConなどのグローバルカンファレンスで定期的に講演を行っています。
マティアスはゲント大学でコンピューター工学の博士号を取得し、そこでアプリケーションの内部動作を隠すためのプログラムの難読化によるアプリケーションセキュリティを学びました。


Think about the last time you were at work, perhaps in a software project team working to an impossible deadline. And then, your manager comes along and says there is some mandatory security training to do, and that it needs to be shoehorned into your workday on top of everything else.
They know it, and you know it. It's a huge PITA, but for compliance reasons, you'll be playing some boring training videos in the background while you keep coding, tuning in and out of both tasks and giving your full attention to neither. This is a common scenario; it's highly disruptive, and it wastes everyone's time. Most security training is too generic, and it's easy to ignore something that bounces in and out of a workday with no real value.
As a company, our goal is to bring a better, more effective type of security training to you, and this is born from knowing exactly what it's like to be disengaged from what the AppSec team tells you is important, when each of your priorities is misaligned. What is interesting, though, is that we started to think about what we could do to reduce the barrier to getting training when you need it - even with our full platform, there are a few steps involved that take you away from your work, at moments where you still need a helpful push but can't dedicate a block of concentration to a training session.
We looked at how micro-learning could be implemented into your workflow, in the IDE or issue tracker, in a more seamless way. And this is what we came up with:
This is based on Just-in-Time (JiT) principles, wherein you're served the right knowledge, at the right time for it to be immediately effective and useful. It's the opposite of the just in case approach to learning, which is often a state of information overload that takes away precious time and headspace for building features.
Quality code is secure code, and if you need a non-invasive security sidekick to collaborate with occasionally, then it might be worth your while to take it for a test drive.
Eliminate the barriers, and bring the training to you.
Cybersecurity might be an interest for some, but not everyone. And no-one should expect developers to become security experts - that still remains the job of specialist AppSec teams. However, security-aware developers are revered for their skills, and the protection they can offer organizations right from the code-building stage. It's a position in high demand, and you can build the foundations over time with contextual micro-learning.
Now, if you're thinking about integrated training as more like Clippy (may he rest in peace), then it's important to note that in the case of Secure Code Warrior's integrations, they're built by developers for developers, so the irritation factor has been considered and obliterated.
Let's check it out in action:

Secure Code Warrior for Github inspects code for Common Weakness Enumeration (CWE) or OWASP references in the labels, issue title, and body of issues to display contextual just-in-time training. The way it works is if a vulnerability reference is found, a comment will be posted on the issue to assist in swift resolution and prevention of recurring vulnerabilities. It integrates with the issue without disruption of your process, or making you jump through hoops for a solution.
And if you use Jira, the process is similar:

Now, for the incumbent security-aware superstars, it's important to remember that it's not all on you to make magic happen. You're going to need support, training, and a reason to take security seriously and get it into your own workflow. Luckily, this is all part of a functioning DevSecOps process, and lots of organizations are already taking note. Why not get a head start?
Download them now, and let us know what you think.

Think about the last time you were at work, perhaps in a software project team working to an impossible deadline. And then, your manager comes along and says there is some mandatory security training to do, and that it needs to be shoehorned into your workday on top of everything else.
They know it, and you know it. It's a huge PITA, but for compliance reasons, you'll be playing some boring training videos in the background while you keep coding, tuning in and out of both tasks and giving your full attention to neither. This is a common scenario; it's highly disruptive, and it wastes everyone's time. Most security training is too generic, and it's easy to ignore something that bounces in and out of a workday with no real value.
As a company, our goal is to bring a better, more effective type of security training to you, and this is born from knowing exactly what it's like to be disengaged from what the AppSec team tells you is important, when each of your priorities is misaligned. What is interesting, though, is that we started to think about what we could do to reduce the barrier to getting training when you need it - even with our full platform, there are a few steps involved that take you away from your work, at moments where you still need a helpful push but can't dedicate a block of concentration to a training session.
We looked at how micro-learning could be implemented into your workflow, in the IDE or issue tracker, in a more seamless way. And this is what we came up with:
This is based on Just-in-Time (JiT) principles, wherein you're served the right knowledge, at the right time for it to be immediately effective and useful. It's the opposite of the just in case approach to learning, which is often a state of information overload that takes away precious time and headspace for building features.
Quality code is secure code, and if you need a non-invasive security sidekick to collaborate with occasionally, then it might be worth your while to take it for a test drive.
Eliminate the barriers, and bring the training to you.
Cybersecurity might be an interest for some, but not everyone. And no-one should expect developers to become security experts - that still remains the job of specialist AppSec teams. However, security-aware developers are revered for their skills, and the protection they can offer organizations right from the code-building stage. It's a position in high demand, and you can build the foundations over time with contextual micro-learning.
Now, if you're thinking about integrated training as more like Clippy (may he rest in peace), then it's important to note that in the case of Secure Code Warrior's integrations, they're built by developers for developers, so the irritation factor has been considered and obliterated.
Let's check it out in action:

Secure Code Warrior for Github inspects code for Common Weakness Enumeration (CWE) or OWASP references in the labels, issue title, and body of issues to display contextual just-in-time training. The way it works is if a vulnerability reference is found, a comment will be posted on the issue to assist in swift resolution and prevention of recurring vulnerabilities. It integrates with the issue without disruption of your process, or making you jump through hoops for a solution.
And if you use Jira, the process is similar:

Now, for the incumbent security-aware superstars, it's important to remember that it's not all on you to make magic happen. You're going to need support, training, and a reason to take security seriously and get it into your own workflow. Luckily, this is all part of a functioning DevSecOps process, and lots of organizations are already taking note. Why not get a head start?
Download them now, and let us know what you think.

以下のリンクをクリックして、このリソースのPDFをダウンロードしてください。
Secure Code Warriorは、ソフトウェア開発ライフサイクル全体にわたってコードを保護し、サイバーセキュリティを最優先とする文化を築くお手伝いをします。アプリケーションセキュリティマネージャ、開発者、CISO、またはセキュリティ関係者のいずれであっても、安全でないコードに関連するリスクを軽減するお手伝いをします。
レポートを表示デモを予約マティアス・マドゥ博士は、セキュリティ専門家、研究者、CTO、セキュア・コード・ウォリアーの共同創設者です。Matias はゲント大学で静的分析ソリューションを中心にアプリケーションセキュリティの博士号を取得しました。その後、米国のFortifyに入社し、開発者が安全なコードを書くのを手伝わずに、コードの問題を検出するだけでは不十分であることに気づきました。これがきっかけで、開発者を支援し、セキュリティの負担を軽減し、顧客の期待を超える製品を開発するようになりました。Team Awesome の一員としてデスクにいないときは、RSA カンファレンス、BlackHat、DefCon などのカンファレンスでプレゼンテーションを行うステージでのプレゼンテーションを楽しんでいます。
Matiasは、15年以上のソフトウェアセキュリティの実務経験を持つ研究者および開発者です。フォーティファイ・ソフトウェアや自身の会社であるセンセイ・セキュリティなどの企業向けにソリューションを開発してきました。マティアスはキャリアを通じて、複数のアプリケーションセキュリティ研究プロジェクトを主導し、それが商用製品につながり、10件以上の特許を取得しています。デスクから離れているときには、マティアスは上級アプリケーション・セキュリティ・トレーニング・コースの講師を務め、RSA Conference、Black Hat、DefCon、BSIMM、OWASP AppSec、BruConなどのグローバルカンファレンスで定期的に講演を行っています。
マティアスはゲント大学でコンピューター工学の博士号を取得し、そこでアプリケーションの内部動作を隠すためのプログラムの難読化によるアプリケーションセキュリティを学びました。
Think about the last time you were at work, perhaps in a software project team working to an impossible deadline. And then, your manager comes along and says there is some mandatory security training to do, and that it needs to be shoehorned into your workday on top of everything else.
They know it, and you know it. It's a huge PITA, but for compliance reasons, you'll be playing some boring training videos in the background while you keep coding, tuning in and out of both tasks and giving your full attention to neither. This is a common scenario; it's highly disruptive, and it wastes everyone's time. Most security training is too generic, and it's easy to ignore something that bounces in and out of a workday with no real value.
As a company, our goal is to bring a better, more effective type of security training to you, and this is born from knowing exactly what it's like to be disengaged from what the AppSec team tells you is important, when each of your priorities is misaligned. What is interesting, though, is that we started to think about what we could do to reduce the barrier to getting training when you need it - even with our full platform, there are a few steps involved that take you away from your work, at moments where you still need a helpful push but can't dedicate a block of concentration to a training session.
We looked at how micro-learning could be implemented into your workflow, in the IDE or issue tracker, in a more seamless way. And this is what we came up with:
This is based on Just-in-Time (JiT) principles, wherein you're served the right knowledge, at the right time for it to be immediately effective and useful. It's the opposite of the just in case approach to learning, which is often a state of information overload that takes away precious time and headspace for building features.
Quality code is secure code, and if you need a non-invasive security sidekick to collaborate with occasionally, then it might be worth your while to take it for a test drive.
Eliminate the barriers, and bring the training to you.
Cybersecurity might be an interest for some, but not everyone. And no-one should expect developers to become security experts - that still remains the job of specialist AppSec teams. However, security-aware developers are revered for their skills, and the protection they can offer organizations right from the code-building stage. It's a position in high demand, and you can build the foundations over time with contextual micro-learning.
Now, if you're thinking about integrated training as more like Clippy (may he rest in peace), then it's important to note that in the case of Secure Code Warrior's integrations, they're built by developers for developers, so the irritation factor has been considered and obliterated.
Let's check it out in action:

Secure Code Warrior for Github inspects code for Common Weakness Enumeration (CWE) or OWASP references in the labels, issue title, and body of issues to display contextual just-in-time training. The way it works is if a vulnerability reference is found, a comment will be posted on the issue to assist in swift resolution and prevention of recurring vulnerabilities. It integrates with the issue without disruption of your process, or making you jump through hoops for a solution.
And if you use Jira, the process is similar:

Now, for the incumbent security-aware superstars, it's important to remember that it's not all on you to make magic happen. You're going to need support, training, and a reason to take security seriously and get it into your own workflow. Luckily, this is all part of a functioning DevSecOps process, and lots of organizations are already taking note. Why not get a head start?
Download them now, and let us know what you think.
目次
マティアス・マドゥ博士は、セキュリティ専門家、研究者、CTO、セキュア・コード・ウォリアーの共同創設者です。Matias はゲント大学で静的分析ソリューションを中心にアプリケーションセキュリティの博士号を取得しました。その後、米国のFortifyに入社し、開発者が安全なコードを書くのを手伝わずに、コードの問題を検出するだけでは不十分であることに気づきました。これがきっかけで、開発者を支援し、セキュリティの負担を軽減し、顧客の期待を超える製品を開発するようになりました。Team Awesome の一員としてデスクにいないときは、RSA カンファレンス、BlackHat、DefCon などのカンファレンスでプレゼンテーションを行うステージでのプレゼンテーションを楽しんでいます。

Secure Code Warriorは、ソフトウェア開発ライフサイクル全体にわたってコードを保護し、サイバーセキュリティを最優先とする文化を築くお手伝いをします。アプリケーションセキュリティマネージャ、開発者、CISO、またはセキュリティ関係者のいずれであっても、安全でないコードに関連するリスクを軽減するお手伝いをします。
デモを予約[ダウンロード]始めるためのリソース
Trust Agent:AI - Secure and scale AI-Drive development
AI is writing code. Who’s governing it? With up to 50% of AI-generated code containing security weaknesses, managing AI risk is critical. Discover how SCW's Trust Agent: AI provides the real-time visibility, proactive governance, and targeted upskilling needed to scale AI-driven development securely.
The Power of OpenText Application Security + Secure Code Warrior
OpenText Application Security and Secure Code Warrior combine vulnerability detection with AI Software Governance and developer capability. Together, they help organizations reduce risk, strengthen secure coding practices, and confidently adopt AI-driven development.
Secure Code Warrior corporate overview
Secure Code Warrior is an AI Software Governance platform designed to enable organizations to safely adopt AI-driven development by bridging the gap between development velocity and enterprise security. The platform addresses the "Visibility Gap," where security teams often lack insights into shadow AI coding tools and the origins of production code.













.png)

