
Cyber Resilience Act Explained: What It Means for Secure by Design Software Development
The Cyber Resilience Act is rapidly becoming a strategic priority – not just for EU-based companies, but for any business selling digital products into the European market. While compliance deadlines extend into 2027, engineering and security teams are already asking hard questions about secure by design practices, vulnerability handling, and development capability.
Unlike many regulations that focus on documentation and audits, the CRA places secure software design and development at the heart of compliance. Organizations that invest early in secure by design capabilities will move into compliance faster – and stand out in a market where product security is becoming a purchasing decision.
What the Cyber Resilience Act Requires
The Cyber Resilience Act (CRA) introduces baseline cybersecurity requirements for most products with a digital component placed on the EU market – including software, operating systems, connected devices, and embedded systems.
More importantly, it shifts where responsibility sits.
Security is no longer only a runtime or operational concern. Under the CRA, it becomes a design and development obligation spanning architecture, implementation, maintenance, and vulnerability handling.
For engineering and security leaders, this means:
- Products must be built according to secure by design principles
- Known vulnerabilities must be prevented where possible and handled effectively
- Organizations must demonstrate that secure development practices are in place
In short: compliance is inseparable from how developers write and maintain code.
Who the CRA Applies To
Although introduced by the EU, the CRA applies to any organization worldwide that places in-scope digital products on the EU market, including:
- Software vendors and SaaS providers whose services function as remote data processing components of covered products
- Manufacturers of digital or connected products
- Importers, distributors, and retailers
- Organizations embedding third-party digital components
For global enterprises, CRA readiness is a cross-border development requirement, not a regional compliance exercise.
Why Organizations Are Starting Now
Key milestones:
- September 2026 – Vulnerability reporting obligations begin
- December 2027 – Full compliance required
On paper, that timeline can look comfortable. In reality, development transformation does not happen in quarters – it happens over years.
Secure by design is not a policy update. It requires:
- Upskilling thousands of development across languages and teams
- Embedding secure by design expectations into day-to-day workflows
- Shifting from reactive vulnerability remediation to prevention
- Creating measurable evidence that secure development practices are consistently applied
These changes affect hiring, onboarding, architecture decisions, SDLC processes, and engineering culture. Organizations that delay until late 2026 will be attempting to retrofit capability under regulatory pressure – a far more expensive and disruptive path.
Enforcement also carries significant financial risk. Under Article 64 of the CRA, penalties can reach €15 million or 2.5% of global annual turnover for violations of essential cybersecurity requirements.
Waiting until late 2026 is simply too late.
CRA Is Ultimately a Developer Capability Challenge
Many regulations focus on policies and documentation. The CRA goes further by linking compliance to the actual practices used to design and build software. It raises expectations around secure development as an operational discipline, not just a governance requirement.
For engineering leaders, this means compliance depends on whether development teams consistently apply secure practices, including:
- Understanding common vulnerability classes
- Applying secure design and architecture principles
- Avoiding insecure implementation patterns
- Handling third-party and open-source components responsibly
Security tooling plays an important role in detecting issues. But tools surface weaknesses after code is written. Secure by design requires developers to prevent vulnerabilities in the first place – and to do so consistently across teams, languages, and products.
Tools alone cannot achieve this. Secure by design outcomes depend on human capability.
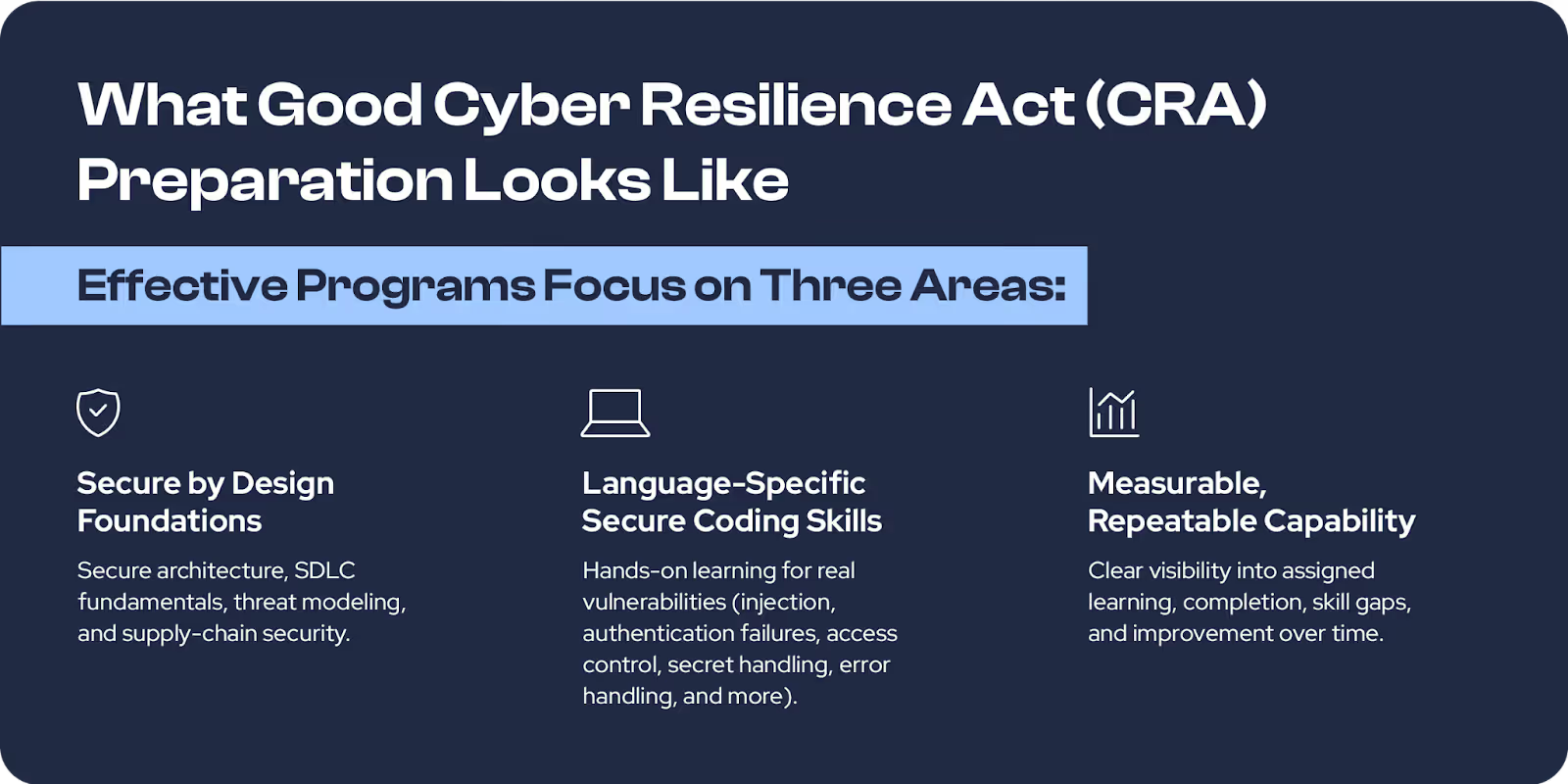
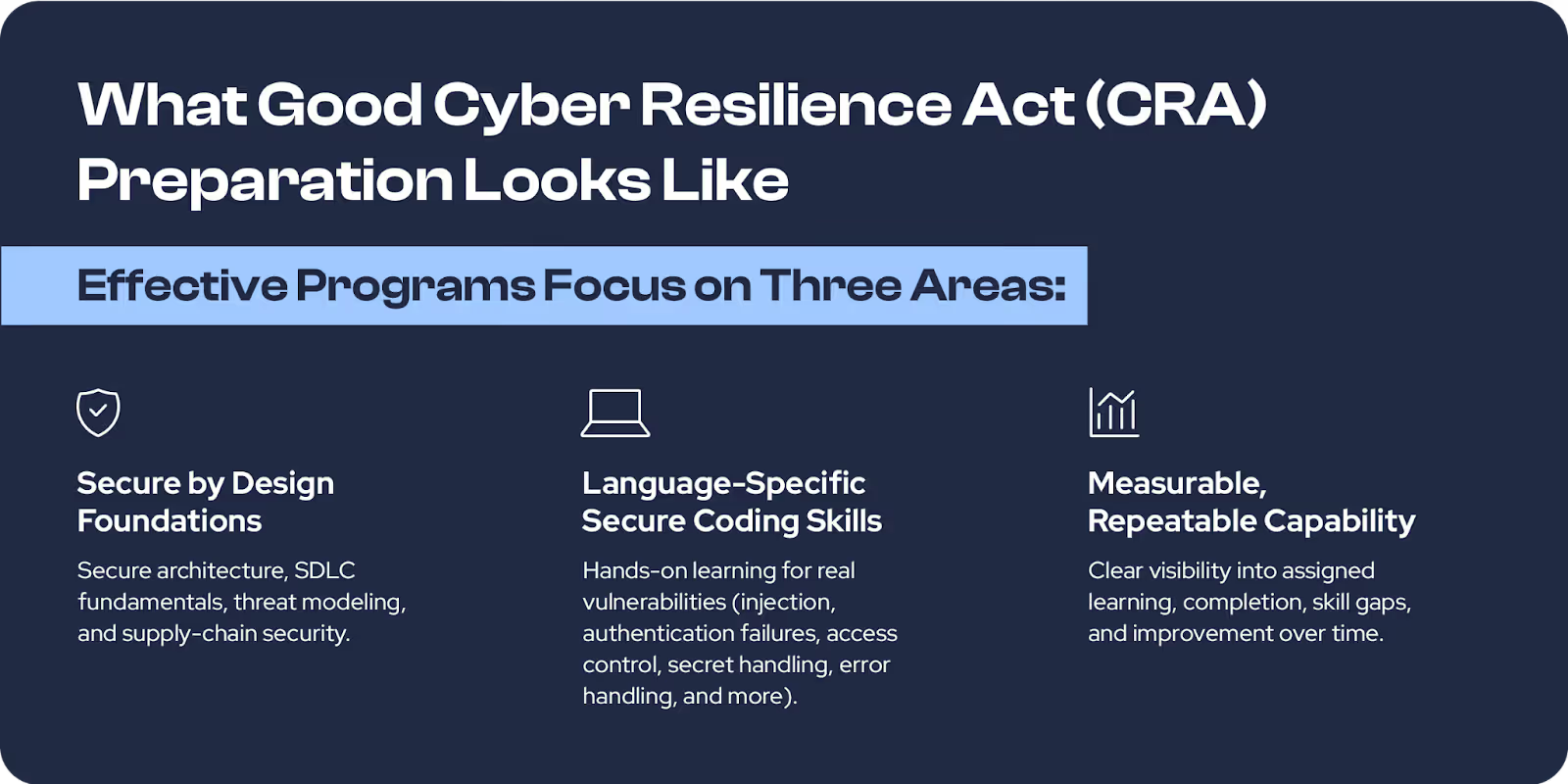
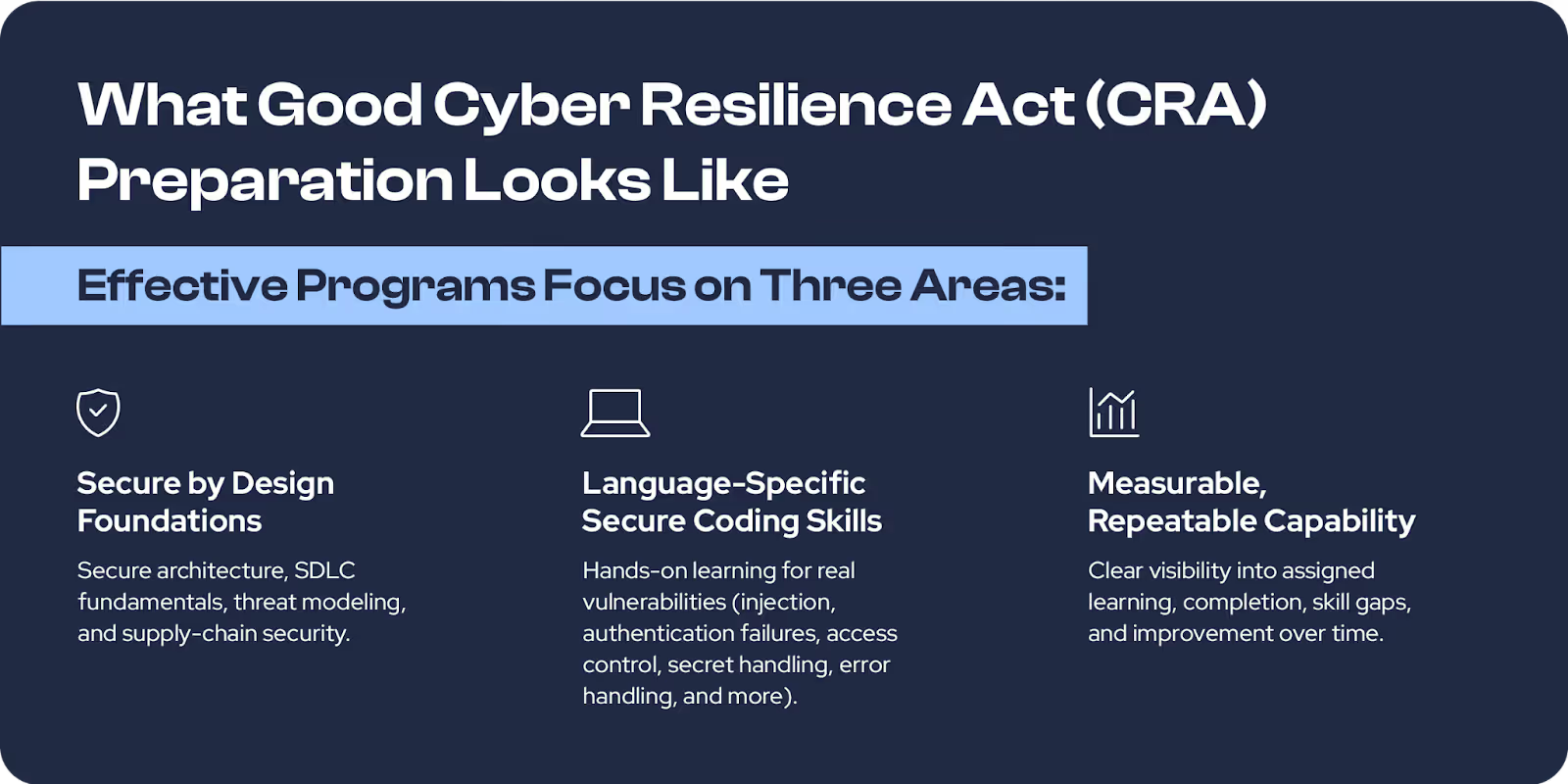
How Secure Code Warrior Supports CRA Readiness
Secure Code Warrior provides CRA-aligned learning pathways that combine:
- A CRA Standard Quest mapped to Annex I, Part I technical vulnerability requirements
- A Secure by Design Conceptual Collection
- Hands-on, language-specific vulnerability learning
Check out our onesheet guide on all of the CRA-Aligned learning content in SCW. SCW does not certify compliance. We support CRA readiness through structured learning and measurable capability improvement aligned to the regulation’s secure development principles.
Start Building CRA Readiness Now
The CRA reflects where the industry is headed: secure by design engineering as the default expectation. Organizations that invest in developer capability now will be better positioned for compliance – and for building more resilient, lower-risk software long term.
For additional details on how Secure Code Warrior can assist you in achieving compliance, check out our knowledge base: How Secure Code Warrior can assist you in achieving compliance


Learn what the EU Cyber Resilience Act (CRA) requires, who it applies to, and how engineering teams can prepare with secure by design practices, vulnerability prevention, and developer capability building.
Shannon Holt is a cybersecurity product marketer with a background in application security, cloud security services, and compliance standards like PCI-DSS and HITRUST.

Secure Code Warrior is here for your organization to help you secure code across the entire software development lifecycle and create a culture in which cybersecurity is top of mind. Whether you’re an AppSec Manager, Developer, CISO, or anyone involved in security, we can help your organization reduce risks associated with insecure code.
Book a demoShannon Holt is a cybersecurity product marketer with a background in application security, cloud security services, and compliance standards like PCI-DSS and HITRUST.
Shannon Holt is a cybersecurity product marketer with a background in application security, cloud security services, and compliance standards like PCI-DSS and HITRUST. She’s passionate about making secure development and compliance more practical and approachable for technical teams, bridging the gap between security expectations and the realities of modern software development.


The Cyber Resilience Act is rapidly becoming a strategic priority – not just for EU-based companies, but for any business selling digital products into the European market. While compliance deadlines extend into 2027, engineering and security teams are already asking hard questions about secure by design practices, vulnerability handling, and development capability.
Unlike many regulations that focus on documentation and audits, the CRA places secure software design and development at the heart of compliance. Organizations that invest early in secure by design capabilities will move into compliance faster – and stand out in a market where product security is becoming a purchasing decision.
What the Cyber Resilience Act Requires
The Cyber Resilience Act (CRA) introduces baseline cybersecurity requirements for most products with a digital component placed on the EU market – including software, operating systems, connected devices, and embedded systems.
More importantly, it shifts where responsibility sits.
Security is no longer only a runtime or operational concern. Under the CRA, it becomes a design and development obligation spanning architecture, implementation, maintenance, and vulnerability handling.
For engineering and security leaders, this means:
- Products must be built according to secure by design principles
- Known vulnerabilities must be prevented where possible and handled effectively
- Organizations must demonstrate that secure development practices are in place
In short: compliance is inseparable from how developers write and maintain code.
Who the CRA Applies To
Although introduced by the EU, the CRA applies to any organization worldwide that places in-scope digital products on the EU market, including:
- Software vendors and SaaS providers whose services function as remote data processing components of covered products
- Manufacturers of digital or connected products
- Importers, distributors, and retailers
- Organizations embedding third-party digital components
For global enterprises, CRA readiness is a cross-border development requirement, not a regional compliance exercise.
Why Organizations Are Starting Now
Key milestones:
- September 2026 – Vulnerability reporting obligations begin
- December 2027 – Full compliance required
On paper, that timeline can look comfortable. In reality, development transformation does not happen in quarters – it happens over years.
Secure by design is not a policy update. It requires:
- Upskilling thousands of development across languages and teams
- Embedding secure by design expectations into day-to-day workflows
- Shifting from reactive vulnerability remediation to prevention
- Creating measurable evidence that secure development practices are consistently applied
These changes affect hiring, onboarding, architecture decisions, SDLC processes, and engineering culture. Organizations that delay until late 2026 will be attempting to retrofit capability under regulatory pressure – a far more expensive and disruptive path.
Enforcement also carries significant financial risk. Under Article 64 of the CRA, penalties can reach €15 million or 2.5% of global annual turnover for violations of essential cybersecurity requirements.
Waiting until late 2026 is simply too late.
CRA Is Ultimately a Developer Capability Challenge
Many regulations focus on policies and documentation. The CRA goes further by linking compliance to the actual practices used to design and build software. It raises expectations around secure development as an operational discipline, not just a governance requirement.
For engineering leaders, this means compliance depends on whether development teams consistently apply secure practices, including:
- Understanding common vulnerability classes
- Applying secure design and architecture principles
- Avoiding insecure implementation patterns
- Handling third-party and open-source components responsibly
Security tooling plays an important role in detecting issues. But tools surface weaknesses after code is written. Secure by design requires developers to prevent vulnerabilities in the first place – and to do so consistently across teams, languages, and products.
Tools alone cannot achieve this. Secure by design outcomes depend on human capability.
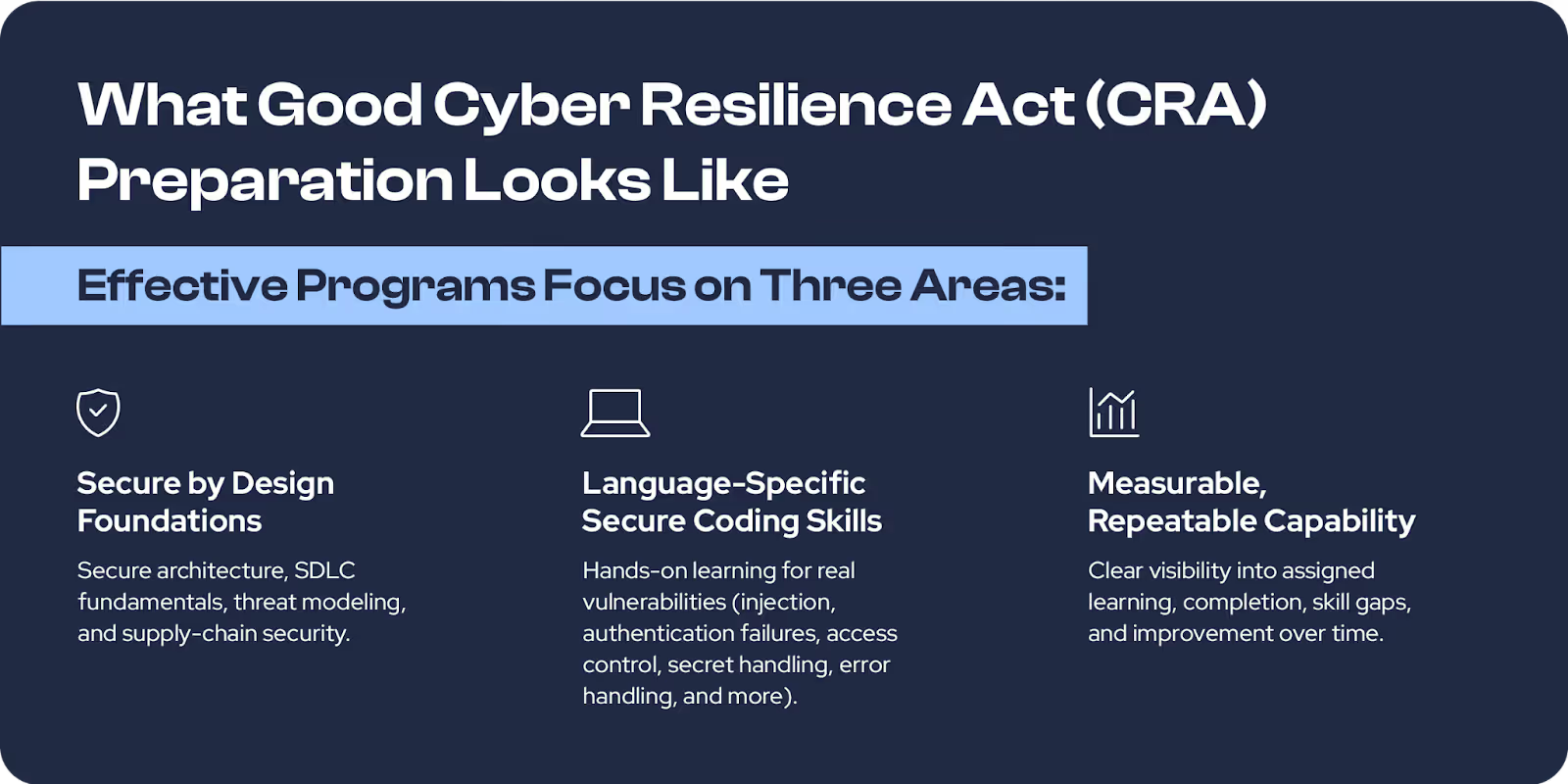
How Secure Code Warrior Supports CRA Readiness
Secure Code Warrior provides CRA-aligned learning pathways that combine:
- A CRA Standard Quest mapped to Annex I, Part I technical vulnerability requirements
- A Secure by Design Conceptual Collection
- Hands-on, language-specific vulnerability learning
Check out our onesheet guide on all of the CRA-Aligned learning content in SCW. SCW does not certify compliance. We support CRA readiness through structured learning and measurable capability improvement aligned to the regulation’s secure development principles.
Start Building CRA Readiness Now
The CRA reflects where the industry is headed: secure by design engineering as the default expectation. Organizations that invest in developer capability now will be better positioned for compliance – and for building more resilient, lower-risk software long term.
For additional details on how Secure Code Warrior can assist you in achieving compliance, check out our knowledge base: How Secure Code Warrior can assist you in achieving compliance

The Cyber Resilience Act is rapidly becoming a strategic priority – not just for EU-based companies, but for any business selling digital products into the European market. While compliance deadlines extend into 2027, engineering and security teams are already asking hard questions about secure by design practices, vulnerability handling, and development capability.
Unlike many regulations that focus on documentation and audits, the CRA places secure software design and development at the heart of compliance. Organizations that invest early in secure by design capabilities will move into compliance faster – and stand out in a market where product security is becoming a purchasing decision.
What the Cyber Resilience Act Requires
The Cyber Resilience Act (CRA) introduces baseline cybersecurity requirements for most products with a digital component placed on the EU market – including software, operating systems, connected devices, and embedded systems.
More importantly, it shifts where responsibility sits.
Security is no longer only a runtime or operational concern. Under the CRA, it becomes a design and development obligation spanning architecture, implementation, maintenance, and vulnerability handling.
For engineering and security leaders, this means:
- Products must be built according to secure by design principles
- Known vulnerabilities must be prevented where possible and handled effectively
- Organizations must demonstrate that secure development practices are in place
In short: compliance is inseparable from how developers write and maintain code.
Who the CRA Applies To
Although introduced by the EU, the CRA applies to any organization worldwide that places in-scope digital products on the EU market, including:
- Software vendors and SaaS providers whose services function as remote data processing components of covered products
- Manufacturers of digital or connected products
- Importers, distributors, and retailers
- Organizations embedding third-party digital components
For global enterprises, CRA readiness is a cross-border development requirement, not a regional compliance exercise.
Why Organizations Are Starting Now
Key milestones:
- September 2026 – Vulnerability reporting obligations begin
- December 2027 – Full compliance required
On paper, that timeline can look comfortable. In reality, development transformation does not happen in quarters – it happens over years.
Secure by design is not a policy update. It requires:
- Upskilling thousands of development across languages and teams
- Embedding secure by design expectations into day-to-day workflows
- Shifting from reactive vulnerability remediation to prevention
- Creating measurable evidence that secure development practices are consistently applied
These changes affect hiring, onboarding, architecture decisions, SDLC processes, and engineering culture. Organizations that delay until late 2026 will be attempting to retrofit capability under regulatory pressure – a far more expensive and disruptive path.
Enforcement also carries significant financial risk. Under Article 64 of the CRA, penalties can reach €15 million or 2.5% of global annual turnover for violations of essential cybersecurity requirements.
Waiting until late 2026 is simply too late.
CRA Is Ultimately a Developer Capability Challenge
Many regulations focus on policies and documentation. The CRA goes further by linking compliance to the actual practices used to design and build software. It raises expectations around secure development as an operational discipline, not just a governance requirement.
For engineering leaders, this means compliance depends on whether development teams consistently apply secure practices, including:
- Understanding common vulnerability classes
- Applying secure design and architecture principles
- Avoiding insecure implementation patterns
- Handling third-party and open-source components responsibly
Security tooling plays an important role in detecting issues. But tools surface weaknesses after code is written. Secure by design requires developers to prevent vulnerabilities in the first place – and to do so consistently across teams, languages, and products.
Tools alone cannot achieve this. Secure by design outcomes depend on human capability.
How Secure Code Warrior Supports CRA Readiness
Secure Code Warrior provides CRA-aligned learning pathways that combine:
- A CRA Standard Quest mapped to Annex I, Part I technical vulnerability requirements
- A Secure by Design Conceptual Collection
- Hands-on, language-specific vulnerability learning
Check out our onesheet guide on all of the CRA-Aligned learning content in SCW. SCW does not certify compliance. We support CRA readiness through structured learning and measurable capability improvement aligned to the regulation’s secure development principles.
Start Building CRA Readiness Now
The CRA reflects where the industry is headed: secure by design engineering as the default expectation. Organizations that invest in developer capability now will be better positioned for compliance – and for building more resilient, lower-risk software long term.
For additional details on how Secure Code Warrior can assist you in achieving compliance, check out our knowledge base: How Secure Code Warrior can assist you in achieving compliance

Click on the link below and download the PDF of this resource.
Secure Code Warrior is here for your organization to help you secure code across the entire software development lifecycle and create a culture in which cybersecurity is top of mind. Whether you’re an AppSec Manager, Developer, CISO, or anyone involved in security, we can help your organization reduce risks associated with insecure code.
View reportBook a demo
Check out our onesheet guide on all of the CRA-Aligned learning content in SCW.
Download PDFShannon Holt is a cybersecurity product marketer with a background in application security, cloud security services, and compliance standards like PCI-DSS and HITRUST.
Shannon Holt is a cybersecurity product marketer with a background in application security, cloud security services, and compliance standards like PCI-DSS and HITRUST. She’s passionate about making secure development and compliance more practical and approachable for technical teams, bridging the gap between security expectations and the realities of modern software development.
The Cyber Resilience Act is rapidly becoming a strategic priority – not just for EU-based companies, but for any business selling digital products into the European market. While compliance deadlines extend into 2027, engineering and security teams are already asking hard questions about secure by design practices, vulnerability handling, and development capability.
Unlike many regulations that focus on documentation and audits, the CRA places secure software design and development at the heart of compliance. Organizations that invest early in secure by design capabilities will move into compliance faster – and stand out in a market where product security is becoming a purchasing decision.
What the Cyber Resilience Act Requires
The Cyber Resilience Act (CRA) introduces baseline cybersecurity requirements for most products with a digital component placed on the EU market – including software, operating systems, connected devices, and embedded systems.
More importantly, it shifts where responsibility sits.
Security is no longer only a runtime or operational concern. Under the CRA, it becomes a design and development obligation spanning architecture, implementation, maintenance, and vulnerability handling.
For engineering and security leaders, this means:
- Products must be built according to secure by design principles
- Known vulnerabilities must be prevented where possible and handled effectively
- Organizations must demonstrate that secure development practices are in place
In short: compliance is inseparable from how developers write and maintain code.
Who the CRA Applies To
Although introduced by the EU, the CRA applies to any organization worldwide that places in-scope digital products on the EU market, including:
- Software vendors and SaaS providers whose services function as remote data processing components of covered products
- Manufacturers of digital or connected products
- Importers, distributors, and retailers
- Organizations embedding third-party digital components
For global enterprises, CRA readiness is a cross-border development requirement, not a regional compliance exercise.
Why Organizations Are Starting Now
Key milestones:
- September 2026 – Vulnerability reporting obligations begin
- December 2027 – Full compliance required
On paper, that timeline can look comfortable. In reality, development transformation does not happen in quarters – it happens over years.
Secure by design is not a policy update. It requires:
- Upskilling thousands of development across languages and teams
- Embedding secure by design expectations into day-to-day workflows
- Shifting from reactive vulnerability remediation to prevention
- Creating measurable evidence that secure development practices are consistently applied
These changes affect hiring, onboarding, architecture decisions, SDLC processes, and engineering culture. Organizations that delay until late 2026 will be attempting to retrofit capability under regulatory pressure – a far more expensive and disruptive path.
Enforcement also carries significant financial risk. Under Article 64 of the CRA, penalties can reach €15 million or 2.5% of global annual turnover for violations of essential cybersecurity requirements.
Waiting until late 2026 is simply too late.
CRA Is Ultimately a Developer Capability Challenge
Many regulations focus on policies and documentation. The CRA goes further by linking compliance to the actual practices used to design and build software. It raises expectations around secure development as an operational discipline, not just a governance requirement.
For engineering leaders, this means compliance depends on whether development teams consistently apply secure practices, including:
- Understanding common vulnerability classes
- Applying secure design and architecture principles
- Avoiding insecure implementation patterns
- Handling third-party and open-source components responsibly
Security tooling plays an important role in detecting issues. But tools surface weaknesses after code is written. Secure by design requires developers to prevent vulnerabilities in the first place – and to do so consistently across teams, languages, and products.
Tools alone cannot achieve this. Secure by design outcomes depend on human capability.
How Secure Code Warrior Supports CRA Readiness
Secure Code Warrior provides CRA-aligned learning pathways that combine:
- A CRA Standard Quest mapped to Annex I, Part I technical vulnerability requirements
- A Secure by Design Conceptual Collection
- Hands-on, language-specific vulnerability learning
Check out our onesheet guide on all of the CRA-Aligned learning content in SCW. SCW does not certify compliance. We support CRA readiness through structured learning and measurable capability improvement aligned to the regulation’s secure development principles.
Start Building CRA Readiness Now
The CRA reflects where the industry is headed: secure by design engineering as the default expectation. Organizations that invest in developer capability now will be better positioned for compliance – and for building more resilient, lower-risk software long term.
For additional details on how Secure Code Warrior can assist you in achieving compliance, check out our knowledge base: How Secure Code Warrior can assist you in achieving compliance
Table of contents
Shannon Holt is a cybersecurity product marketer with a background in application security, cloud security services, and compliance standards like PCI-DSS and HITRUST.

Secure Code Warrior is here for your organization to help you secure code across the entire software development lifecycle and create a culture in which cybersecurity is top of mind. Whether you’re an AppSec Manager, Developer, CISO, or anyone involved in security, we can help your organization reduce risks associated with insecure code.
Book a demoDownloadResources to get you started
SCW Learning Content for KnowBe4
Secure Code Warrior content available through KnowBe4 helps technical teams build secure coding and AI governance awareness through structured learning covering OWASP Top 10 risks, AI-assisted development, and modern secure coding practices.
Trust Agent:AI - Secure and scale AI-Drive development
AI is writing code. Who’s governing it? With up to 50% of AI-generated code containing security weaknesses, managing AI risk is critical. Discover how SCW's Trust Agent: AI provides the real-time visibility, proactive governance, and targeted upskilling needed to scale AI-driven development securely.
Resources to get you started
Equipping Developers for the Generative AI Era: AWS Collaboration
I am proud to announce that Secure Code Warrior has signed a strategic collaboration agreement with Amazon Web Services (AWS). Given the rapid evolution of the threat landscape, this strategic collaboration could not come at a more mission-critical moment for both security leaders and future-focused developers.
Securing the Future of Software: SCW and KnowBe4 Join Forces
I am thrilled to announce today an upcoming strategic partnership between Secure Code Warrior and KnowBe4. KnowBe4 is a world-renowned leader in comprehensively managing human and agentic AI risk, making them the perfect partner to help us distribute foundational security awareness to organizations across the globe.














